Bulletproftlink - A phishing service from Malaysia (Part 3)
How lucrative is being a phishing service operator? How the facade of his professional life look like? Today, we review how much money can be made with phishing in merely two years and how large the Bulletproftlink operation is.
This is a multipart article. In the last part of the series (Part 1, Part 2), we look into the life of a professional bulletproof server hosting owner and the scale of his phishing operation.
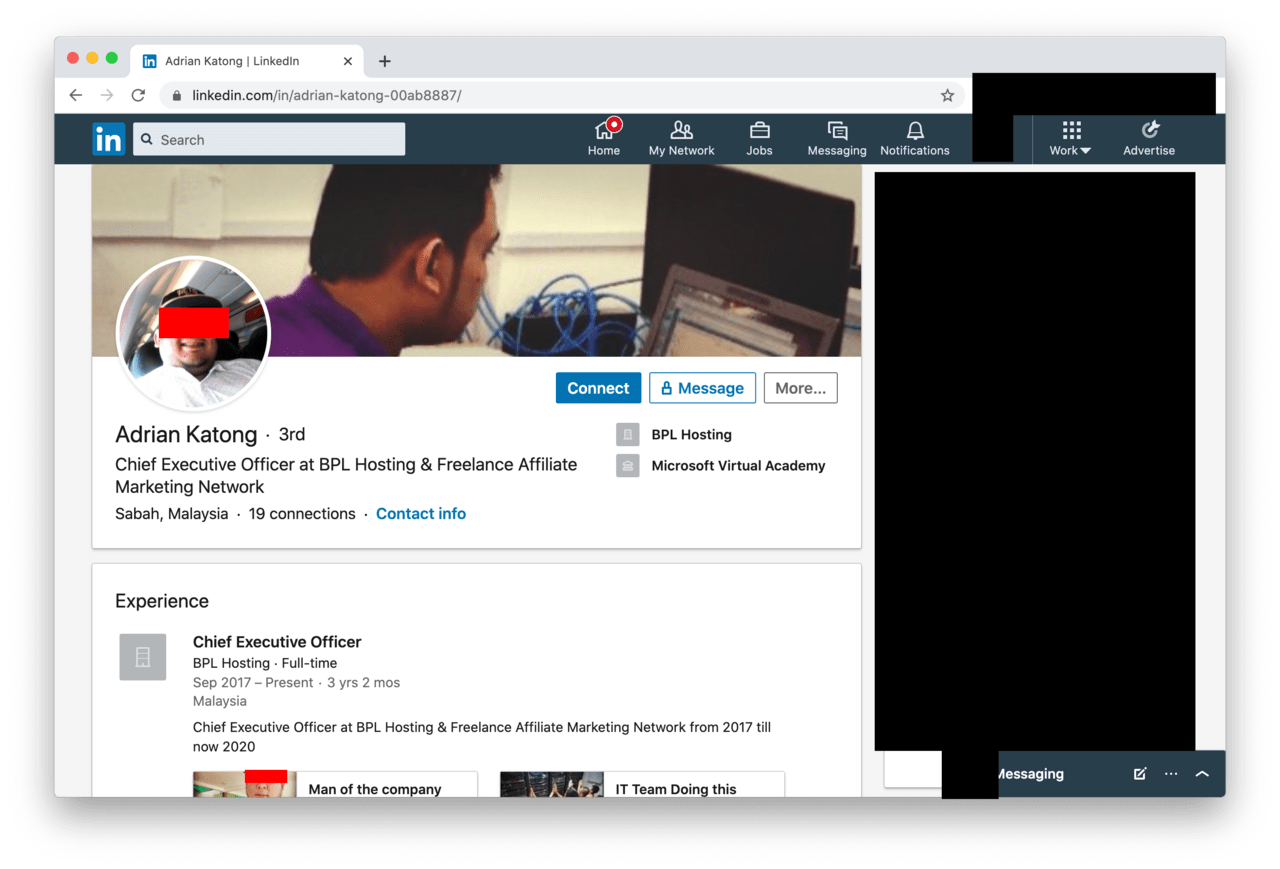
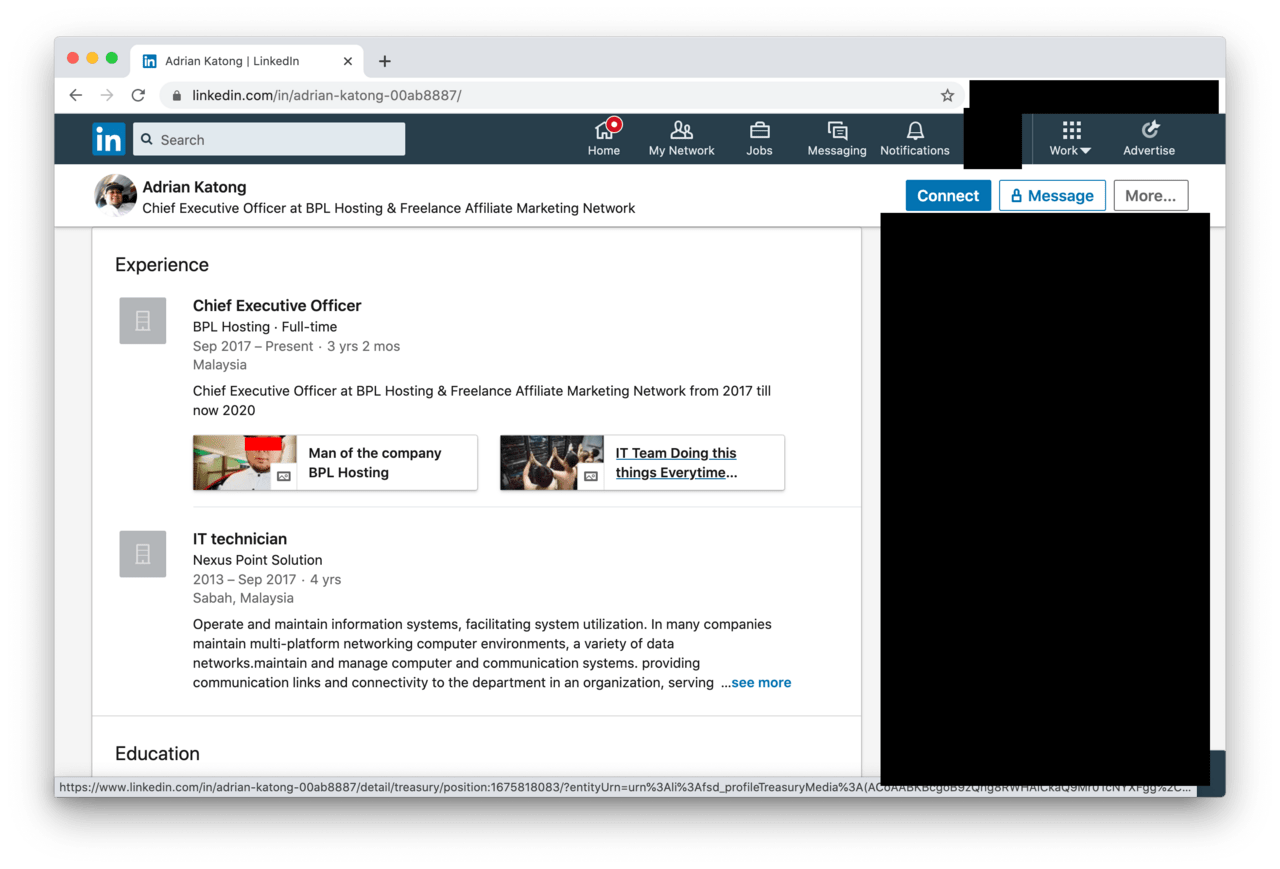
Professional life
In the previous parts of this series, we established that Adrian Katong appear to have close ties with Anthrax Linkers, an adversary group running phishing operations. We also found that Bulletproftlink (also tied to Anthrax Linkers) is a webshop offering various phishing products and bulletproof hosting services.
According to Mr Katong’s public LinkedIn profile, he claims to be the CEO of a company named ‘BPL Hosting’. As we did not manage to find any legitimate business running under this name, we assume that ‘BPL’ likely stands for ‘BulletProftLink’.
The profile page also reveals that Mr Katong works in Sabah, Malaysia. Remember the ties to 7Heaven LLC (7h.com.ua) in Kyiv, Ukraine? Adrian Katong merely relies on no-questions-asked server hosting providers from Ukraine for his phishing services, but he runs his business from Malaysia.
According to his work history, he worked for ‘Nexus Point Solution’ between 2013 and 2017. His responsibilities included the ‘maintenance and operation of large networks and computer systems’ meaning Mr Katong has the technical skills as well as experience to operate a business like Bulletproftlink.
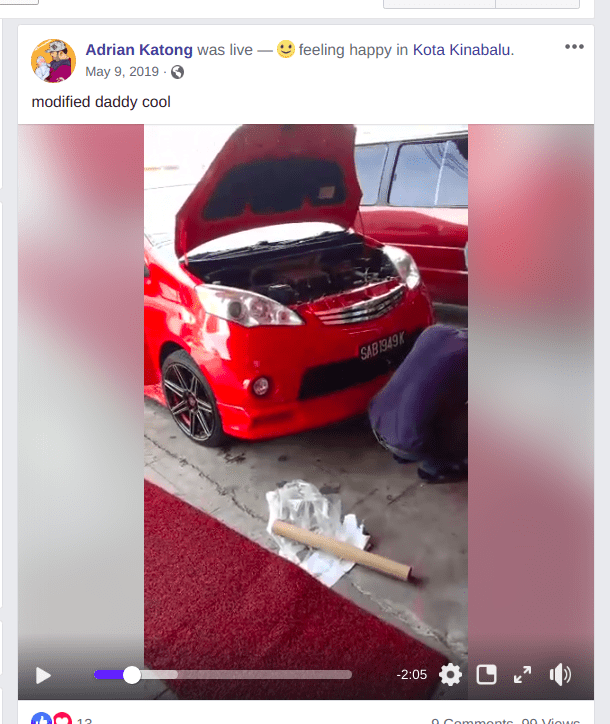
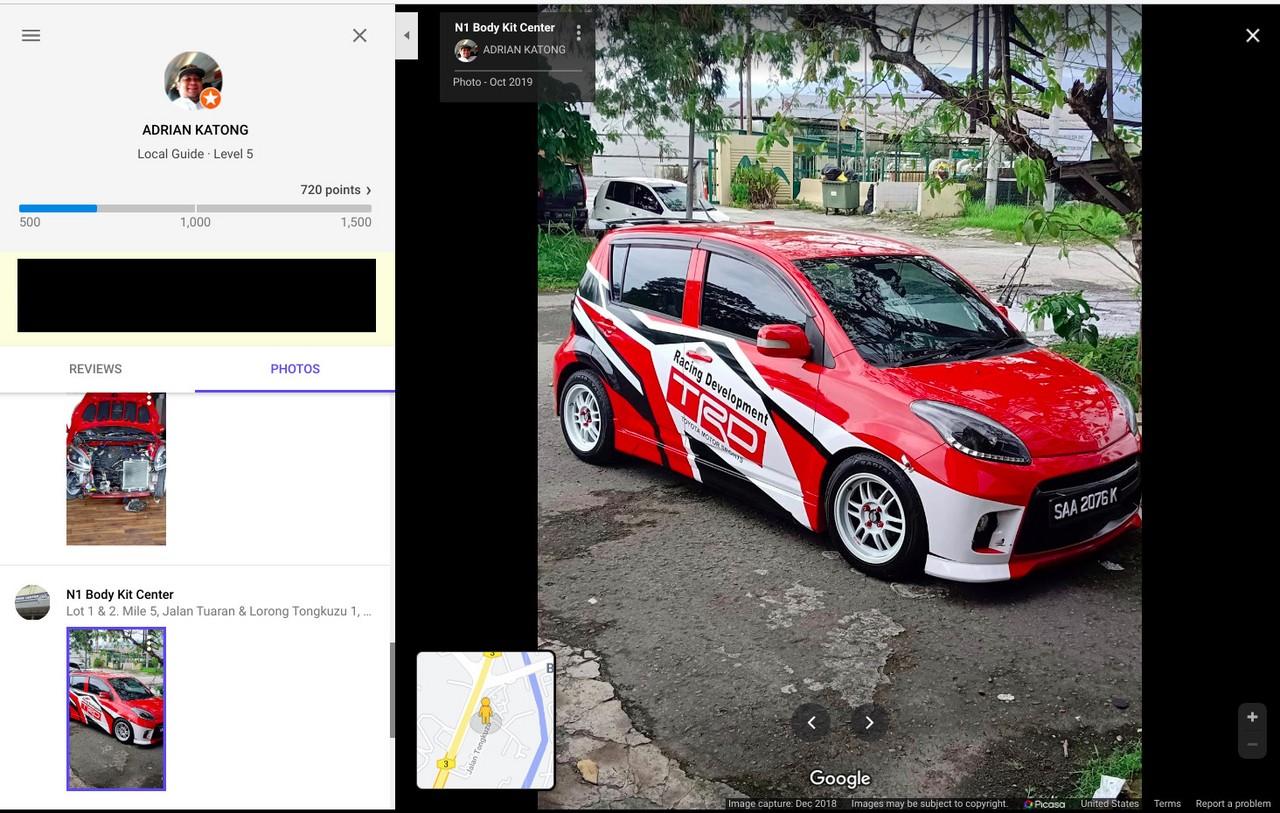
A luxurious lifestyle
Mr Katong and his family have a relatively public life on social media, allowing us to peek into the personal life of the owner of a phishing service operator.
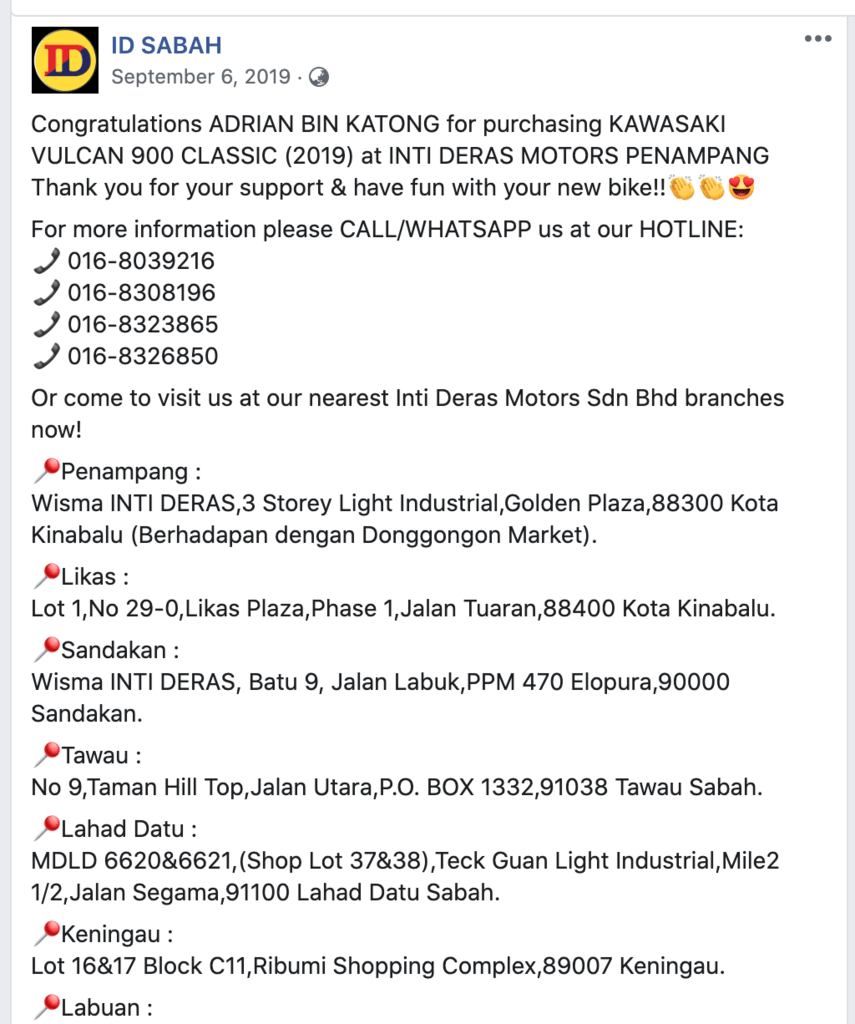
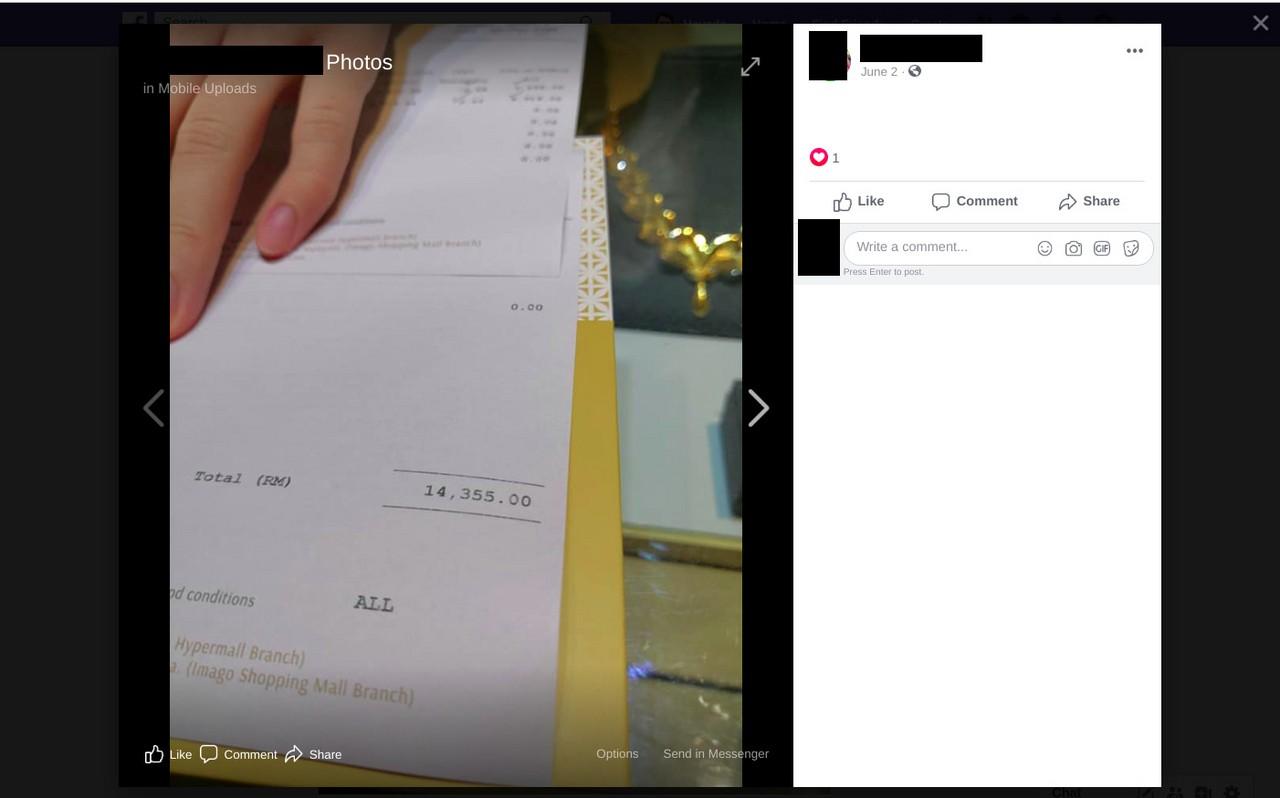
According to the public social media, Mr Katong purchased several cars in the past few years, including two heavily-customised compact cars, a Toyota family car. As one of his hobbies is motorbikes, he purchased a Kawasaki Vulcan 900 Classic motorbike in 2019.
Mr Katong also likes to treat his family well, as he likes to spoil his spouse with luxury items such as designer wear and jewellery according to the photos on his Facebook page.
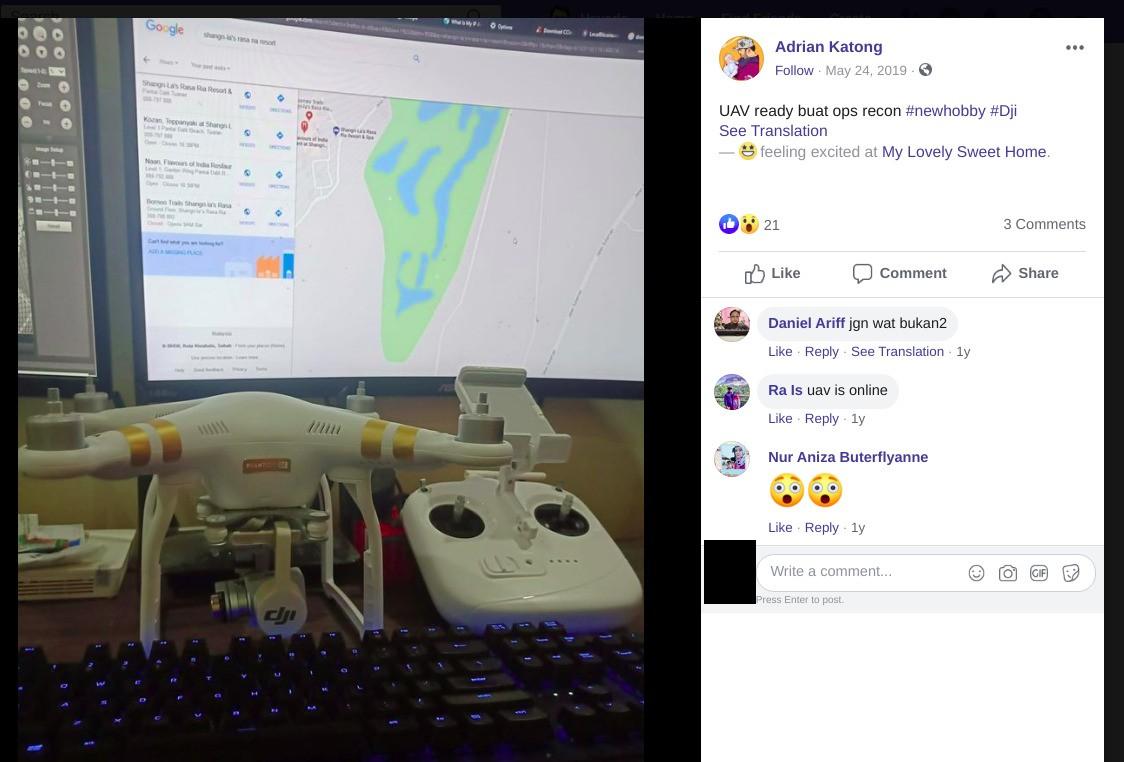
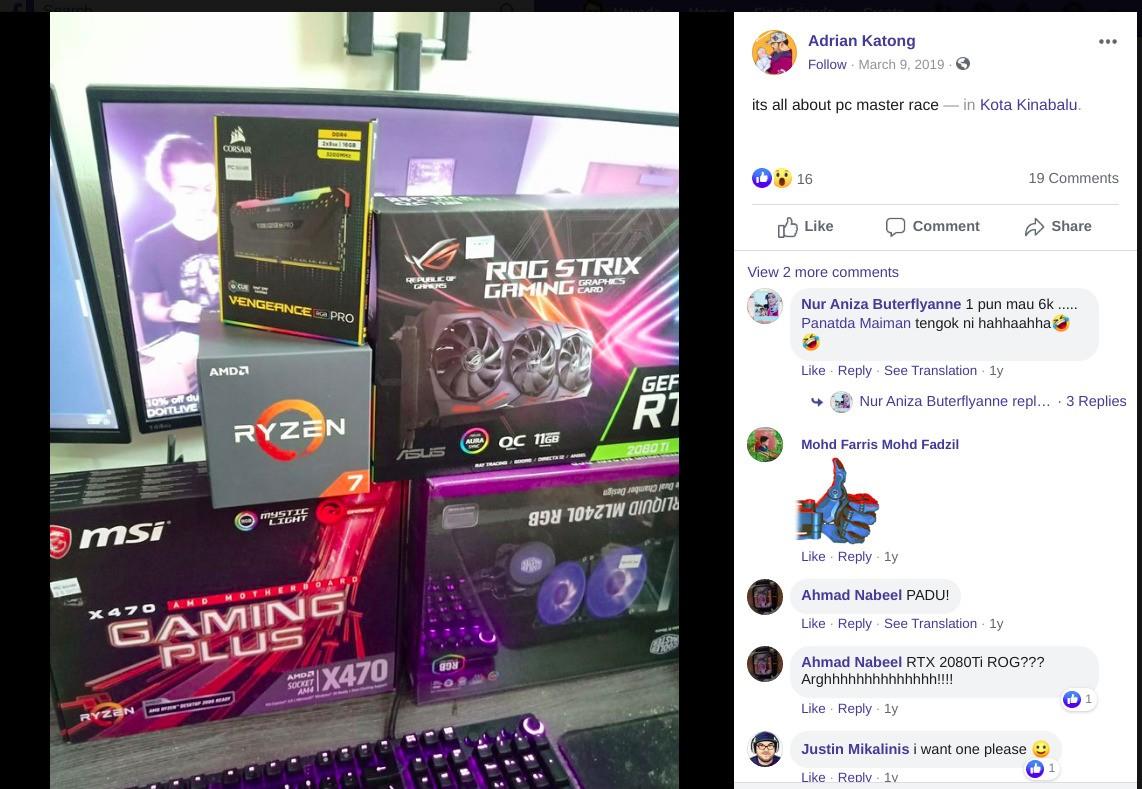
Adrian Katong seem to spend some serious cash on tech gadgets as well. He purchased a drone, a new computer and a surveillance system recently according to the following public posts on Facebook.
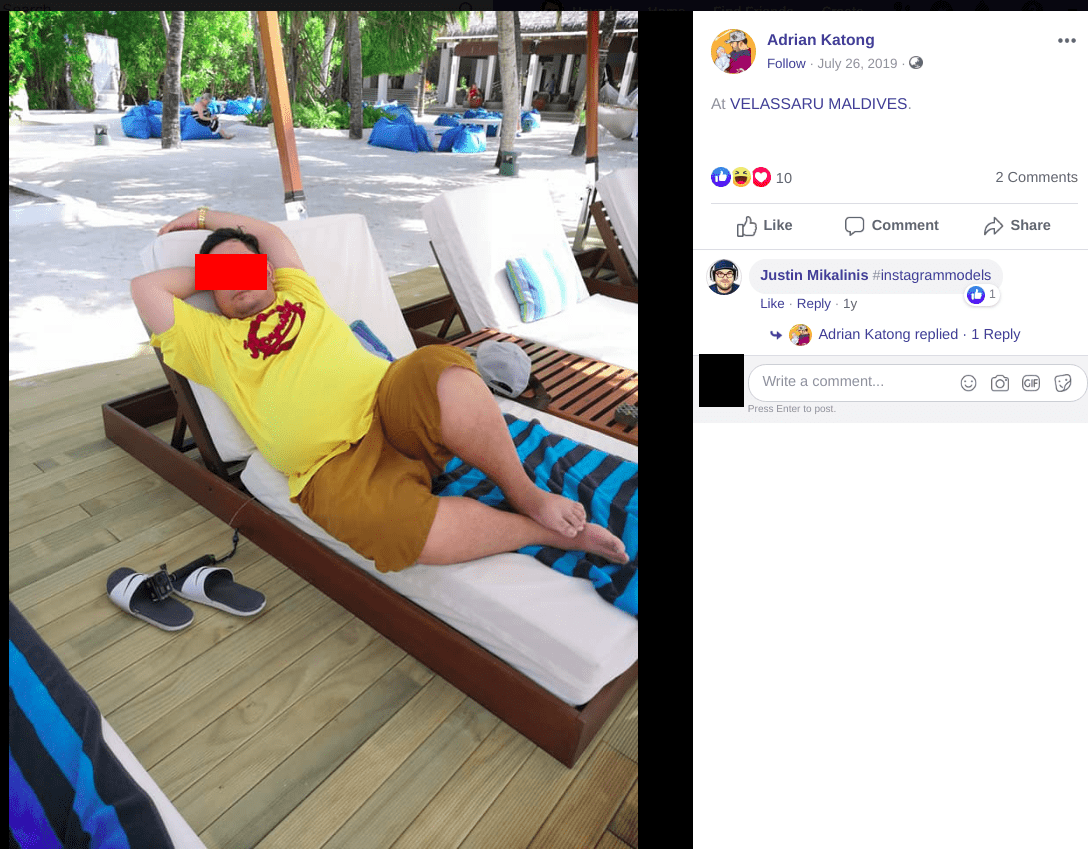
Per other social media posts, the family took extravagant trips to Thailand and the Maldives in the past couple of years.
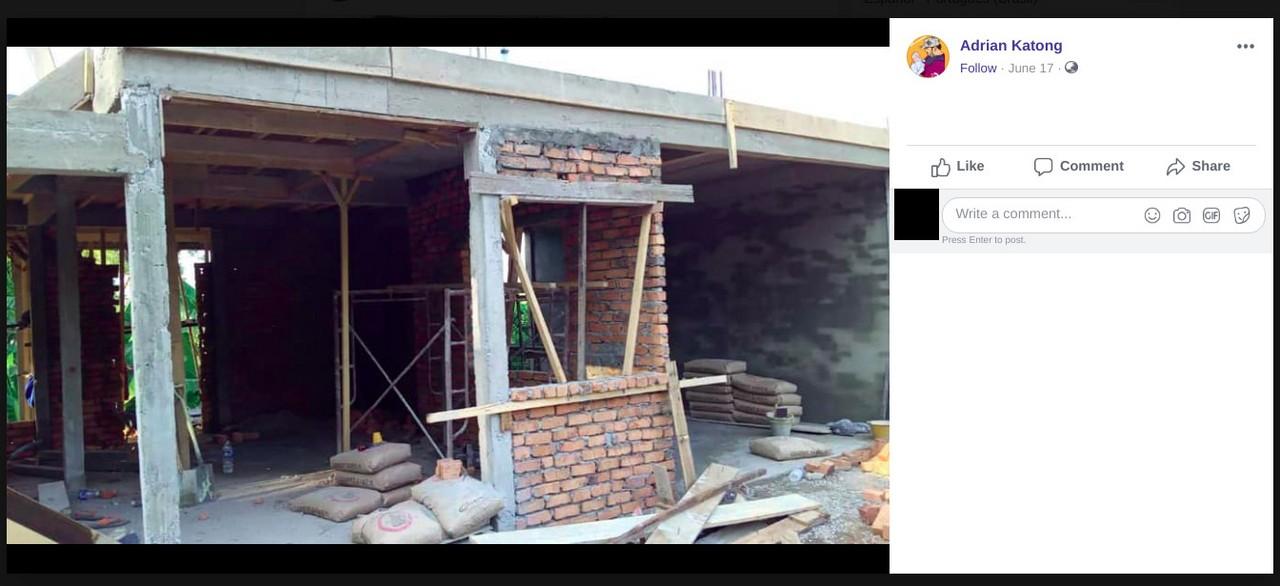
Lastly, a new family house is being built this year in parallel with these splurges from above.
According to public data, we found no evidence that the person claiming to be Mr Katong had any second source of income apart from his own IT operation. In other words, all these binges are all presumably financed by Mr Katong’s CEO ‘salary’ at BPL hosting.
We also could not help but notice that these purchases were all made in 2019 and 2020. As a reminder, Bulletproftlink is coincidentally offering its illegitimate services since mid-2018 according to Internet Archive records.
The sheer scale of the operation
At the time of writing, the scam business at Bulletproftlink is flourishing. The webshop currently features 108 phishing page templates in total up for sale and ready for self-hosting.
The Bulletproftlink password capturing infrastructure includes the following endpoints:
apiserverdata1.com
baller.top
datacenter01.us
f1smtp.com
ghostsmtp.com
gpxsmtp.com
gurl101.services
hostprivate.us
josmtp.com
link101.bid
linuxsmtp.com
migration101.us
panelsmtp.com
racksmtp.com
rosmtp.com
rxasmtp.com
thegreenmy87.com
vitme.bid
voksmtp.com
winsmtp.com
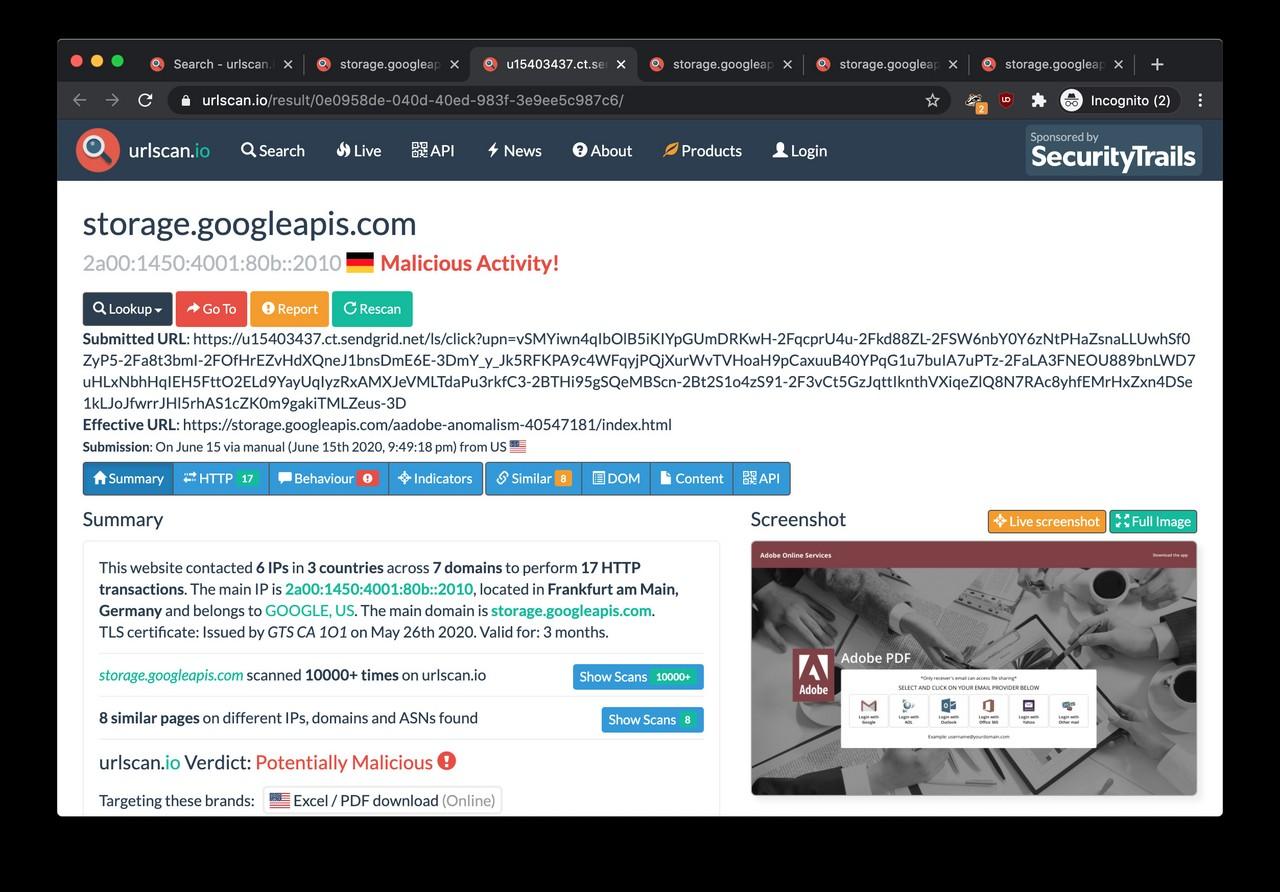
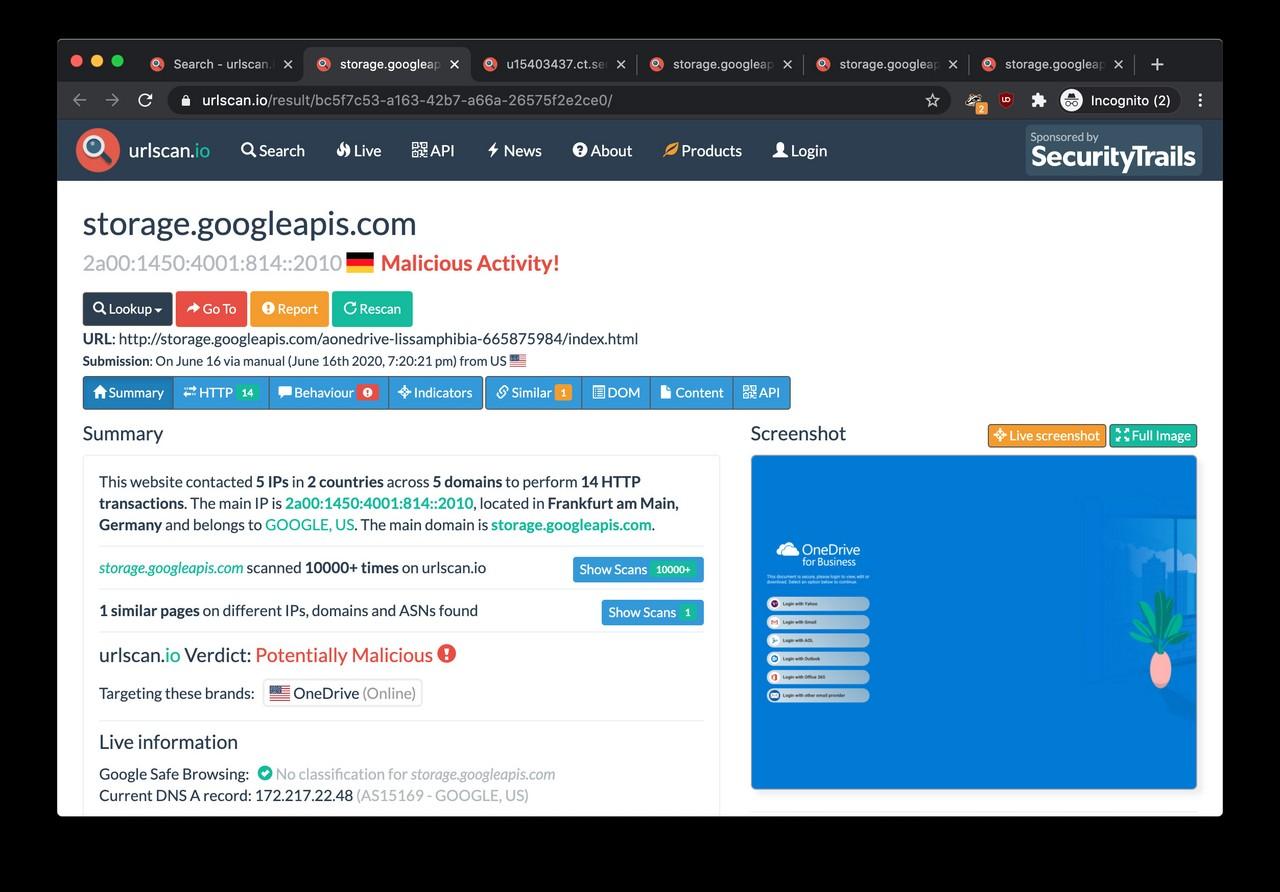
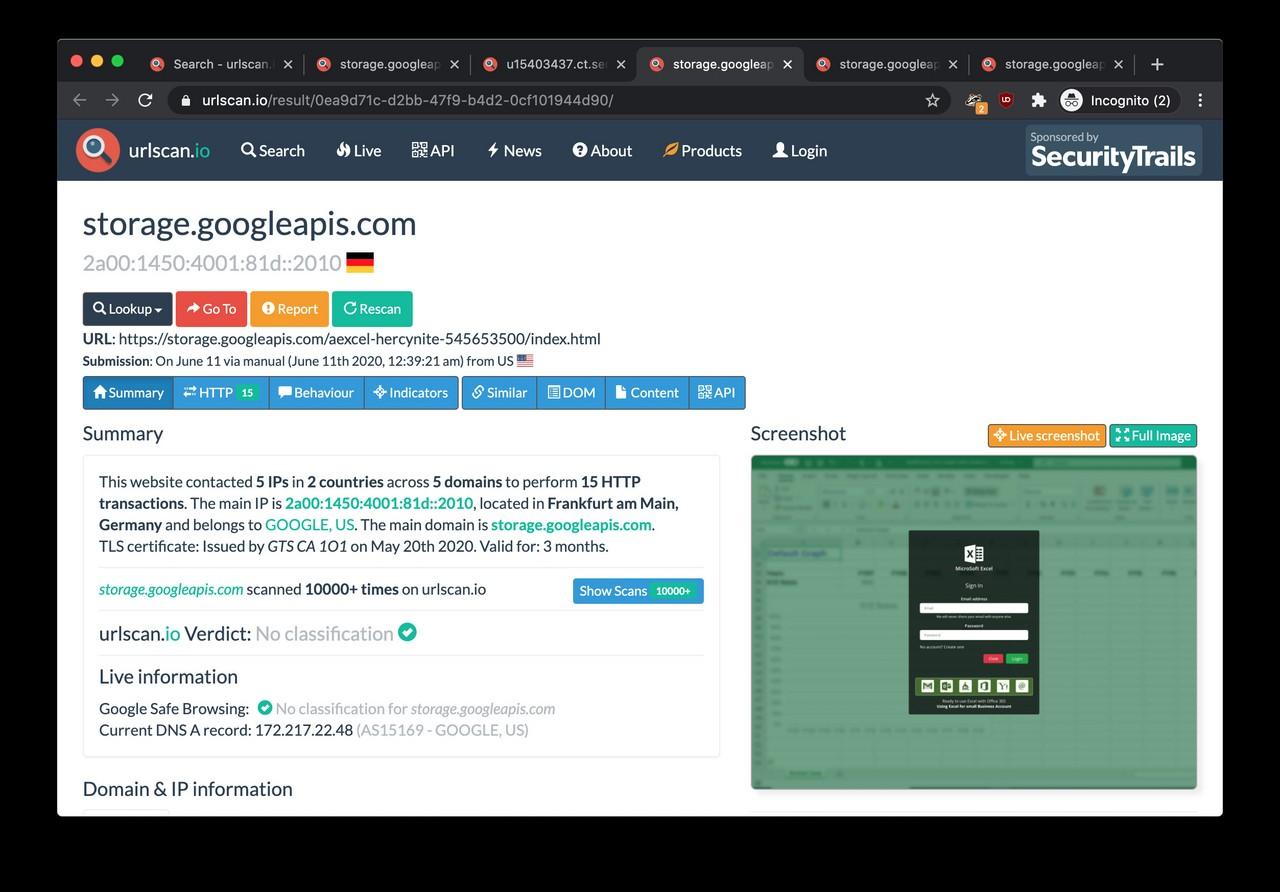
Each password capturing endpoint is associated with a 50-300 fake login pages sending the stolen credentials back to one of these domain names. The phishing pages are typically hosted on the Google Cloud Storage platform.
Random examples
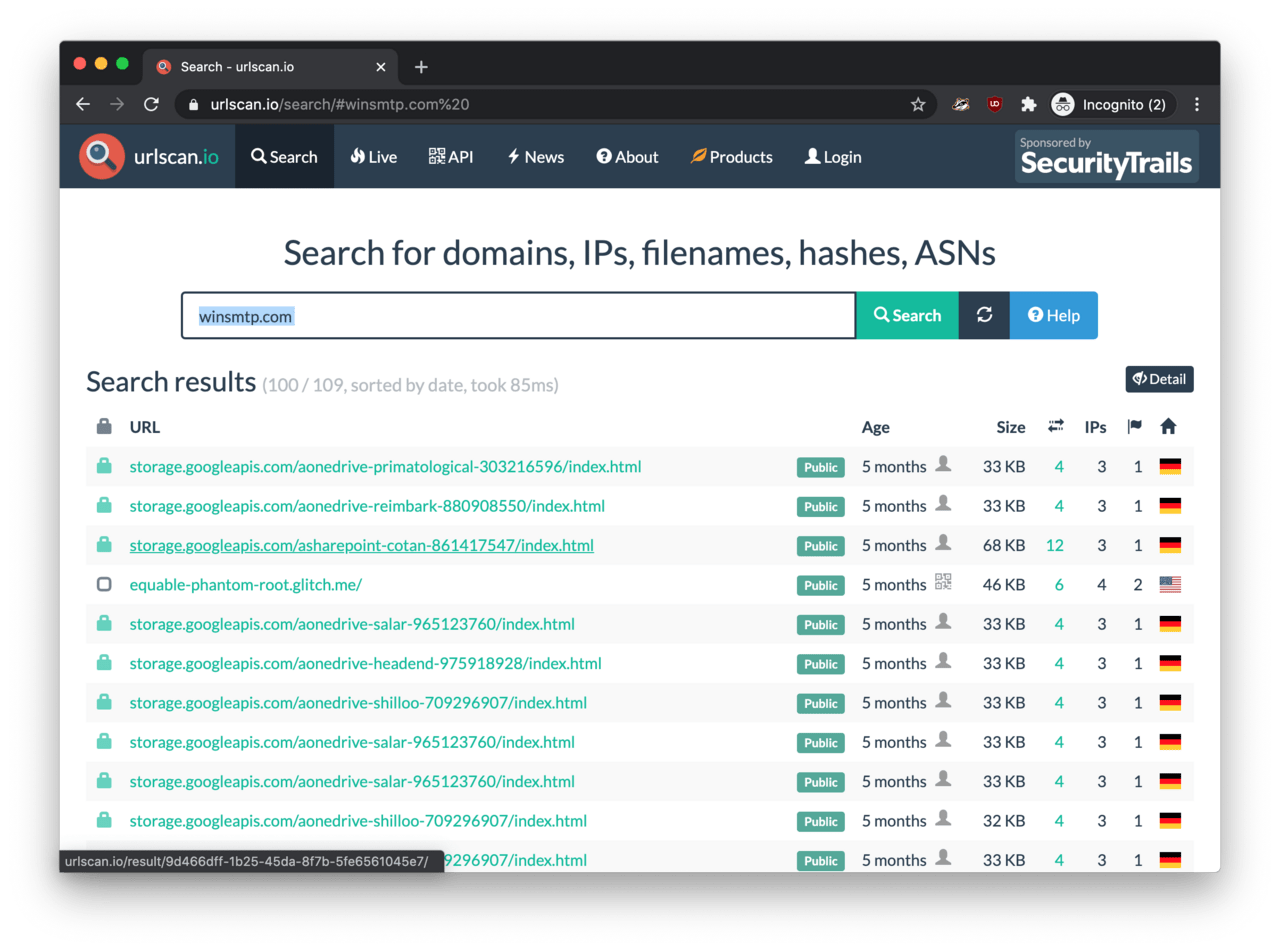
For example, the winsmtp.com endpoint has been seen capturing passwords for at least one-hundred phishing pages according to urlscan.io. The actual number is probably higher.
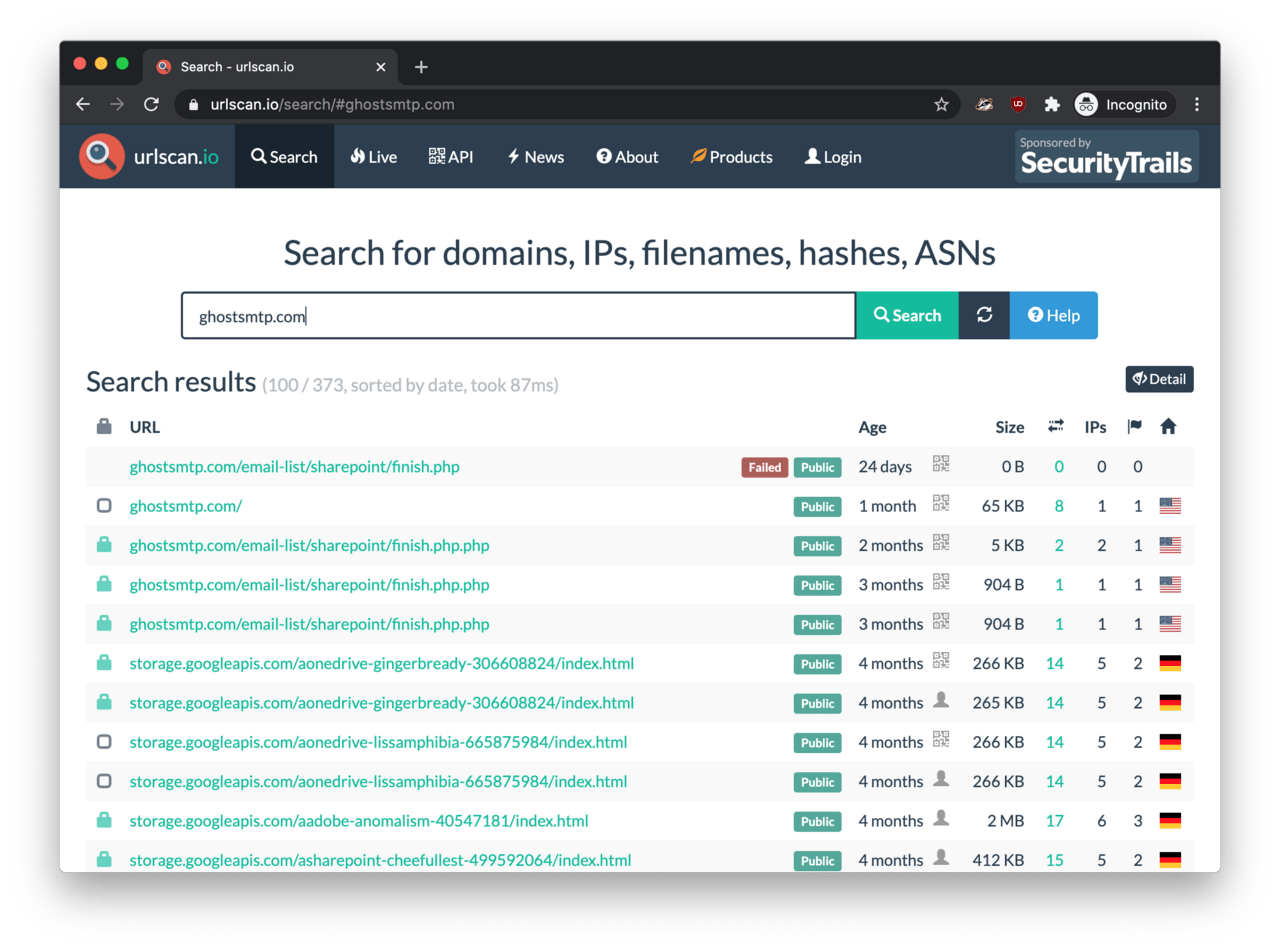
The domain ghostsmtp.com seem to be associated with over 370 phishing pages waiting for the victims to hand over their login credentials unwittingly.
At the end of this article, we list all password capturing URIs and all phishing page links we managed to track down.
Further phishing domains
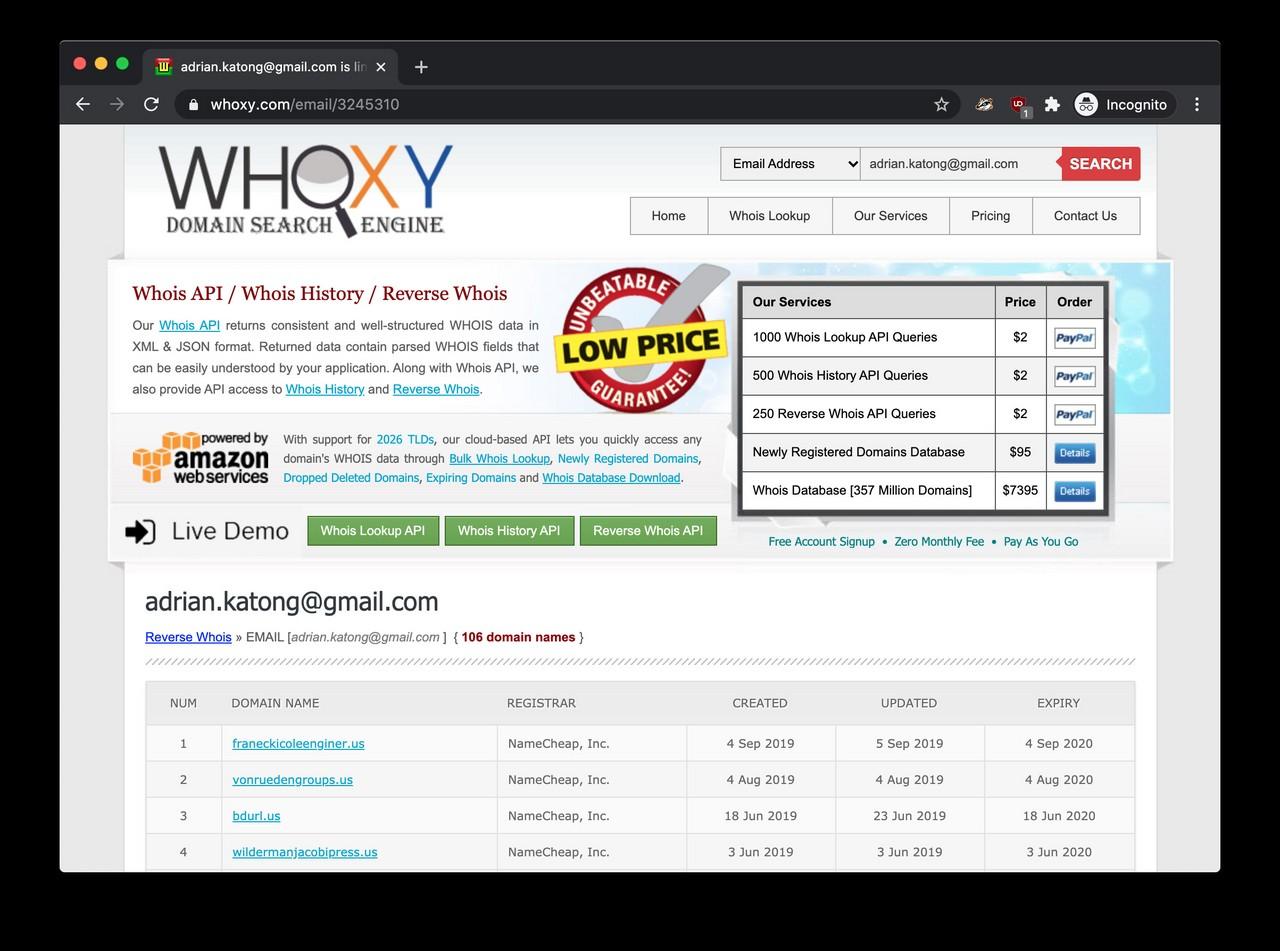
Beside the Anthrax Linkers alter-ego, someone also registered a large number of domain names in the past with the adrian.katong@gmail.com email address. By searching in public WHOIS records, we identified over a 100 domain names featuring this email address as a contact person.
The issue is that these domain names are also associated with phishing activity. For example, arch123.us and lvisurl.us were both serving deceptive login pages respectively - according to Maltiverse and this blog.
Conclusion
By going through the social media posts of the last ten years of someone claiming to be ‘Adrian Katong’ on Facebook, we could not help but notice how a smart and talented computer-enthusiast had slowly turned to cybercrime over the years. The man showed genuine interest in computer security and programming, but he ended up wasting his talent as a phishing service operator selling bulletproof hosting for $800 per month.
Although this hacker’s story may be saddening, let’s not forget the large number of victims whose life turned into hell. The victims’ login passwords likely ended up on the black market for just a few dollars a pop. For instance, the Bulletproftlink ICQ group chat is currently having 1,618 members - all potential buyers of the stolen passwords and the Bulletproftlink phishing services.
As a reminder, the Bulletproftlink services are targeting personal mailboxes and online banking services - both are common ingredients of identity theft. According to the Department of Home Affairs (AU), victims of identity theft lose $4,101 on average, with losses ranging between $1 and $310,000. Apart from financial loss, victims tend to suffer a significant amount of emotional distress as well.
In parallel with the publication of this article, links to the series are sent to the authorities at the FBI Internet Crime Complaint Center (IC3) and MyCERT.
IOCs
Public social media profiles of the individual claiming to be ‘Adrian Katong’ from ‘Anthrax Linkers’ and ‘Bulletproftlink’:
https://www.facebook.com/Adrian.org/
https://www.linkedin.com/in/adrian-katong-00ab8887/
https://www.instagram.com/Serbiggy
https://www.youtube.com/channel/UC9MzzoI1GxM6VmSqvQ20K2w
http://en.gravatar.com/adriankatong
https://steamcommunity.com/id/adriankatong
https://steamid.uk/profile/76561198082708706
https://www.reddit.com/user/adriankatong/
https://www.freelancer.com/u/adriankatong
https://www.twitch.tv/adriankatong
https://twitter.com/adriankatong
http://en.gravatar.com/adriankatong
https://medium.com/@adriankatong
https://dribbble.com/adriankatong/about
https://audiojungle.net/user/adriankatong
https://github.com/thegreenmy87
http://en.gravatar.com/thegreenmy87
Email addresses:
adrian.katong@gmail.com
anthrax.linkers@aol.com
anthrax.linkers@outlook.com
anthrax.win32@yahoo.com
anthrax@secmailbox.net
cynlovn@gmail.com
dgramhot@aol.com
gentle_taral@yahoo.com
rachthomass@msn.com
simbarrt@sabbo.com
staff@dro.xyz
thegreenmy87@gmail.com
thegreenmy@aol.com
thegreenmy@gmail.com
thegreenmy@yahoo.com
Other communication channels:
Telegram: @anthraxlinkers
Jabber: anthraxlinkers@jabb.im
ICQ: 670672280
ICQ: anthraxlinkers
ICQ: anthraxlinkers2
ICQ group chat: https://icq.im/AoLEi6J90MFpQq0Q62g
Skype: live:7d2efe75c20f7e74
Scam operation websites:
https://bulletproftlink.com/
https://www.bulletproftlink.shop/
Home address (unconfirmed):
(available upon request for the relevant cybercrime authorities)
Domains names registered by Adrian Katong:
101cheaphost.us
101datasecurity.us
accessweb101.us
amazinghost101.us
americasafehosting.us
apexwebaccess101.us
aweurl.us
bdurl.us
cheaphost101.us
cheaphosting101.us
dataprovide.us
daurl.us
dawnhost101.us
dfga.us
domainhostworld.us
domainworldhost.us
dusklight101.us
eaccess-vendorsreg.us
easyaccess101.us
easyhost101.us
expanded3rdgeneration.us
fasttransfer101.us
franeckicoleenginer.us
freelancer101world.us
freelancerworld101.us
ghsturl.us
hmeurl.us
hostamazing101.us
hostboxdrop101.us
hostcheap101.us
hostdomainworld.us
hostingcheap101.us
hostingsafeamerica.us
hostlightening101.us
hostnewweb.us
hostwww101.us
httpswww101.us
infomation-center.us
internettech100.us
lighteninghost101.us
local-offices.us
localhomeoffice.us
lvisurl.us
maketrasferfast.us
micro-offices.us
networklogic101.us
networkofweb101.us
networksol101.us
office365-emails.us
office365-home.us
office365-mails.us
office365-outlook.us
officehome.us
officeurl.us
phoenixhosting.us
prodata101.us
safehostamerica.us
securedata101.us
server-office.us
techmails100.us
techmind100.us
the-webworkers.us
theweb-workers.us
thewebworkers101.us
vendor-resgistration.us
vendorresgistration.us
vonruedengroups.us
webaccess101.us
webhostamerica.us
webtechmind100.us
webworld110.us
wildermanjacobipress.us
wingourl.us
worldhost101.us
worldofdomains.us
worldoffreelancer101.us
wwwhost101.us
wwwhttps101.us
Password capturing endpoint URIs:
http://datacenter01.us/adomine420/finish62.php
http://panelsmtp.com/U-lHg0h56qqYYrszFZlyxE4CnrIXT5PoD5JylZCuFIfuE47HvEjFxkfJiiAX/finish8208dfa81b22dbc15f2fbb26f8ec5355bf7e16942f96b0dbbf1af07e820f0d02.php
http://panelsmtp.com/email-list/onedrive-ar/finish.php
http://racksmtp.com/email-list/finish.php
http://rosmtp.com/email-list/onedrive23/finish.php
http://voksmtp.com/tIfrbIXg7ocIv9BcUcJl76Big-9ftuKcdrhI6rt7OOGOe96jUh2CQVR9SHBiYs7YKXA/finish818178bfcc17a8b9665bb54d5c4d97f4b2eb44430790c9a8da87d0814473e28b.php%22
https://apiserverdata1.com/email-list/finish-unv2.php
https://apiserverdata1.com/email-list/office1-true2/handler.php
https://apiserverdata1.com/email-list/office1/finish.php
https://datacenter01.us/adomine420/finish53.php
https://datacenter01.us/andymcoll10/finish72.php
https://datacenter01.us/andymcoll10/finish74.php
https://datacenter01.us/andymcoll10/finish80.php
https://datacenter01.us/dalaighjane/finish393.php
https://datacenter01.us/draco82827/finish104.php
https://datacenter01.us/fshared001/finish2.php
https://datacenter01.us/lucraneee/finish226.php
https://datacenter01.us/moneyboxresult/finish23.php
https://datacenter01.us/officialceo7/finish104.php
https://datacenter01.us/rednecknbb/finish2.php
https://f1smtp.com/XFYCgldG7ZDwT4Tonx7-Ytqre34z4JC_Y2HtB3_4TeXmX9oKCboIr5Pa2lLj/finishef3d35a1e5bf240c2011be9462af4ff21635ce98e586254f31da2d49287d5187.php
https://ghostsmtp.com/email-list/adobe20/finish.php
https://ghostsmtp.com/email-list/sharepoint/finish.php
https://ghostsmtp.com/email-list/sharepoint/finish.php.php
https://gpxsmtp.com/email-list/finish-unv2.php?phishing-processor
https://gpxsmtp.com/email-list/office1-true2/handler.php?phishing-processor
https://gpxsmtp.com/email-list/office1/finish.php?phishing-processor
https://gpxsmtp.com/email-list/onedrive23/finish.php?phishing-processor
https://linuxsmtp.com/FLvkAkuldPWt9i4Q02gGbIZfRHAlUAArkMtToxzhjs3SC0HAITtpfV0PtNnwI9UcVH5E/finish2cec7339231f9cdf64beec8f65526a9a85ea3230c25f9c044a41e23e5ae9c8e9.php?phishing-processor
https://linuxsmtp.com/FLvkAkuldPWt9i4Q02gGbIZfRHAlUAArkMtToxzhjs3SC0HAITtpfV0PtNnwI9UcVH5E/finish6a279f1b41e76da39cff934b7b9f84d719c8cf4b0040575dcacbad56cf88c729.php?phishing-processor
https://linuxsmtp.com/FLvkAkuldPWt9i4Q02gGbIZfRHAlUAArkMtToxzhjs3SC0HAITtpfV0PtNnwI9UcVH5E/finish9761fdf32d8f427130ec638a11cecba3186b674f068e4e1e3259eb557b056c0d.php?phishing-processor
https://linuxsmtp.com/GHzEVfqLU1vhLqs40CPZH4svu7cdluTHWF1h2hTL9S3YMNwYTYMbLVh5UVhz_hiHvA/finish09a7a93aafa569e9112e3d9653e2ca254d53b5bbbc0d3393bd07b370eb68f609.php?phishing-processor
https://linuxsmtp.com/email-list/adobe20/finish.php?phishing-processor
https://linuxsmtp.com/email-list/finish-unv2.php?phishing-processor
https://panelsmtp.com/RhHgwRTISfOtEDp2cPlGvSWrJWBA1YmYopSDPF5uEmXskAUhQsc_Z9ny7Uk5rRkIITRlgw/finish17f17e03419801379f7cc30761ea2fdc25aac70080efda415ba174da20120849.php
https://panelsmtp.com/T9P0k_5yndAClD0M1klyloOJ2x9W_AIQqMXyj_YbOPs6uPliBkCXCXvyhTZotnqG/finish154b4ac47913bf808643552bfbf22e6055c08465149a16e149fd099706cb6e45.php
https://racksmtp.com/1/aaa-all/extf/send/finish2.php
https://racksmtp.com/email-list/domain-au1/finish.php
https://racksmtp.com/email-list/sharepoint/finish.php
https://racksmtp.com/l5rha5dml5ygsmk7ge2tmnbonzqxg5lcmfsxq4dsmvzxgmzribtw2yljnqxgg33n/finish5a8c30ad60df6139e353a817b8ac6520aa71ac92106287373d03c3f096d65989.php?phishing-processor
https://rosmtp.com/KoGGrWyqgq8DUGEFgu0--9bjDryMHxA-2kVyy7p26oJnlgChhh6f4EFcePZD/finishc7f60dc4be52782flfc7317a743f7c5276ca3a1452794f012467f92db1cd3c19.php
https://rosmtp.com/email-list/finish-unv2.php
https://rosmtp.com/email-list/office1-true2/handler.php
https://voksmtp.com/email-list/finish-unv2.php?phishing-processor
https://voksmtp.com/email-list/officenewnew/close.php?phishing-processor
https://winsmtp.com/email-list/excel/finish.php
Phishing pages hosted on Google Cloud Storage:
http://storage.googleapis.com/achase-uncompassionateness-563882333/access.html
http://storage.googleapis.com/alinkedin-leontiasis-214527927/index.html
http://storage.googleapis.com/aonedrive-25-carvene-45557260/index.html
http://storage.googleapis.com/aonedrive-25-grinning-982302530/index.html
http://storage.googleapis.com/aonedrive-25-lushburg-803797168/index.html
http://storage.googleapis.com/aonedrive-25-regian-781460028/index.html
http://storage.googleapis.com/aonedrive-25-remigrates-216934452/index.html
http://storage.googleapis.com/aonedrive-aldehydes-169254050/index.html
http://storage.googleapis.com/aonedrive-assentive-604684136/index.html
http://storage.googleapis.com/aonedrive-electrophone-253132260/index.html
http://storage.googleapis.com/aonedrive-epitomizer-25575182/index.html
http://storage.googleapis.com/aonedrive-heroner-677316791/index.html
http://storage.googleapis.com/aonedrive-indexation-476194097/index.html
http://storage.googleapis.com/aonedrive-interjecting-874489133/GMA.html
http://storage.googleapis.com/aonedrive-interjecting-874489133/index.html
http://storage.googleapis.com/aonedrive-lissamphibia-665875984/index.html
http://storage.googleapis.com/aonedrive-monadistic-624237482/index.html
http://storage.googleapis.com/aonedrive-subtractor-508123424/index.html
http://storage.googleapis.com/aonedrive-taled-172955438/index.html
http://storage.googleapis.com/aonedrive-tapisser-710304904/index.html
http://storage.googleapis.com/aonedrive-windmilled-566078693/index.html
http://storage.googleapis.com/aourtime-necessarily-896797016/index.html
http://storage.googleapis.com/aoutlook-amniorrhea-17875895/index.html
http://storage.googleapis.com/aoutlook-antitubercular-297922690/index.html
http://storage.googleapis.com/aoutlook-centuplication-397143691/index.html
http://storage.googleapis.com/aoutlook-concordatum-329285300/index.html
http://storage.googleapis.com/aoutlook-cytosines-737408570/index.html
http://storage.googleapis.com/aoutlook-hydrophthalmus-376610461/index.html
http://storage.googleapis.com/aoutlook-phalangigrady-490790886/index.html
http://storage.googleapis.com/aoutlook-picrites-965741408/index.html
http://storage.googleapis.com/aoutlook-scotist-58775533/index.html
http://storage.googleapis.com/asharepoint-prospers-214761571/OTHER.html
http://storage.googleapis.com/asharepoint-weirdwoman-991244860/index.html
https://s3-api.us-geo.objectstorage.softlayer.net/aoffice365-miersite-909815082/aoffice365-miersite-909815082/portal-office-login-2.html
https://storage.googleapis.com/aadobe-absolutest-299644311/index.html
https://storage.googleapis.com/aadobe-aclinal-21332609/index.html
https://storage.googleapis.com/aadobe-anomalism-40547181/index.html
https://storage.googleapis.com/aadobe-boldnesses-241925319/index.html
https://storage.googleapis.com/aadobe-dezinced-638369722/index.html
https://storage.googleapis.com/aadobe-extrospection-817200196/index.html
https://storage.googleapis.com/aadobe-fentanyl-96619567/index.html
https://storage.googleapis.com/aadobe-furazane-938987195/index.html
https://storage.googleapis.com/aadobe-genets-102385273/index.html
https://storage.googleapis.com/aadobe-gymnurinae-904416409/index.html
https://storage.googleapis.com/aadobe-inhabitant-239448763/index.html
https://storage.googleapis.com/aadobe-plied-252595259/index.html
https://storage.googleapis.com/aadobe-provinculum-964198444/index.html
https://storage.googleapis.com/aadobe-sportsmanship-225828423/index.html
https://storage.googleapis.com/aadobe-tuberculosed-431696714/index.html
https://storage.googleapis.com/aadobe-tulips-961252399/index.html
https://storage.googleapis.com/aadobe-unwire-956063317/index.html
https://storage.googleapis.com/aadobe-urosome-766946619/index.html
https://storage.googleapis.com/aadobe-venturer-662042129/index.html
https://storage.googleapis.com/abox-callose-708580235/index.html
https://storage.googleapis.com/abox-skyscrapers-213162800/index.html
https://storage.googleapis.com/abox-sobful-892522313/OTHER.html
https://storage.googleapis.com/achase-liberalise-875285190/access.html?cmd=login_submit&id=
https://storage.googleapis.com/adocusign-autogauge-554602584/index.html
https://storage.googleapis.com/adocusign-myzodendraceous-779715893/index.html
https://storage.googleapis.com/adocusign-nonsyncopation-597545102/index.html
https://storage.googleapis.com/adocusign-visionlike-406109160/index.html
https://storage.googleapis.com/adropbox-adolph-216452570/index.html
https://storage.googleapis.com/adropbox-attercrop-335736963/warn1.html
https://storage.googleapis.com/adropbox-canadite-991414134/index.html
https://storage.googleapis.com/adropbox-castillo-590462409/GMA-validate.html
https://storage.googleapis.com/adropbox-columbella-713166418/index.html
https://storage.googleapis.com/adropbox-crummier-951272531/GMA-validate.html
https://storage.googleapis.com/adropbox-degustate-931936837/index.html
https://storage.googleapis.com/adropbox-maunna-854152331/index.html
https://storage.googleapis.com/adropbox-pauraque-229414766/log.html
https://storage.googleapis.com/adropbox-rundowns-605949893/log.html
https://storage.googleapis.com/adropbox-slaggiest-162559818/index.html
https://storage.googleapis.com/adropbox-tetrahydrofuran-138813919/index.html
https://storage.googleapis.com/aexcel-garden-519223751/index.html
https://storage.googleapis.com/aexcel-hercynite-545653500/index.html
https://storage.googleapis.com/aexcel-keratonyxis-780671813/index.html
https://storage.googleapis.com/aexcel-overcleave-701706490/index.html
https://storage.googleapis.com/aexcel-peritonsillitis-846813081/index.html
https://storage.googleapis.com/aexcel-pickableness-962802557/index.html
https://storage.googleapis.com/aexcel-prosaicness-858157497/index.html
https://storage.googleapis.com/aexcel-reintegrate-986985627/index.html
https://storage.googleapis.com/aexcel-rowths-792239398/index.html
https://storage.googleapis.com/aexcel-slote-278679275/index.html
https://storage.googleapis.com/aexcel-topology-876768729/index.html
https://storage.googleapis.com/ageneral-webmail-2-unsolidarity-190556987/index.html
https://storage.googleapis.com/alinkedin-dewater-687062852/index.html
https://storage.googleapis.com/all-owa/live.htm
https://storage.googleapis.com/aoffice365-fatstock-400891649/index2.html
https://storage.googleapis.com/aoffice365-seductionist-113741681/index2.html
https://storage.googleapis.com/aoffice365-trapperlike-392012627/index2.html
https://storage.googleapis.com/aonedrive-25-academized-698386455/index.html
https://storage.googleapis.com/aonedrive-25-anting-581279920/index.html
https://storage.googleapis.com/aonedrive-25-bistipulate-372282379/index.html
https://storage.googleapis.com/aonedrive-25-caesalpinia-153375838/index.html
https://storage.googleapis.com/aonedrive-25-carvene-45557260/index.html
https://storage.googleapis.com/aonedrive-25-demivirgin-183747005/index.html
https://storage.googleapis.com/aonedrive-25-divestment-415325444/index.html
https://storage.googleapis.com/aonedrive-25-double-login-azoic-943128002/index.html
https://storage.googleapis.com/aonedrive-25-double-login-overdecking-586161423/index.html
https://storage.googleapis.com/aonedrive-25-double-login-overempty-479469798/index.html
https://storage.googleapis.com/aonedrive-25-double-login-rosa-50398731/GMA.html
https://storage.googleapis.com/aonedrive-25-double-login-rosa-50398731/OTHER.html
https://storage.googleapis.com/aonedrive-25-double-login-rosa-50398731/index.html
https://storage.googleapis.com/aonedrive-25-double-login-scarcy-941388921/index.html
https://storage.googleapis.com/aonedrive-25-grinning-982302530/index.html
https://storage.googleapis.com/aonedrive-25-heptoxide-353018933/index.html
https://storage.googleapis.com/aonedrive-25-interventional-743113675/index.html
https://storage.googleapis.com/aonedrive-25-isize-290846352/index.html
https://storage.googleapis.com/aonedrive-25-lherzolite-767384449/index.html
https://storage.googleapis.com/aonedrive-25-olympics-424188436/index.html
https://storage.googleapis.com/aonedrive-25-oppilative-109616622/index.html
https://storage.googleapis.com/aonedrive-25-patrogenesis-340077410/index.html
https://storage.googleapis.com/aonedrive-25-phenalgin-754372542/index.html
https://storage.googleapis.com/aonedrive-25-poppywort-869144369/index.html
https://storage.googleapis.com/aonedrive-25-procomment-245584736/index.html
https://storage.googleapis.com/aonedrive-25-pylangium-940273628/index.html
https://storage.googleapis.com/aonedrive-25-querulosity-976526005/index.html
https://storage.googleapis.com/aonedrive-25-recementation-330244758/index.html
https://storage.googleapis.com/aonedrive-25-regian-781460028/index.html
https://storage.googleapis.com/aonedrive-25-roupit-644238688/index.html
https://storage.googleapis.com/aonedrive-25-schizophreniac-240261123/index.html
https://storage.googleapis.com/aonedrive-25-scoptophilic-536811198/index.html
https://storage.googleapis.com/aonedrive-25-swimmy-386441626/index.html
https://storage.googleapis.com/aonedrive-25-undivestedly-680774501/index.html
https://storage.googleapis.com/aonedrive-25-unmovingly-439335872/index.html
https://storage.googleapis.com/aonedrive-academia-746262876/index.html
https://storage.googleapis.com/aonedrive-aftercataract-260936781/index.html
https://storage.googleapis.com/aonedrive-alliterativeness-414767671/index.html
https://storage.googleapis.com/aonedrive-almogavar-577542574/index.html
https://storage.googleapis.com/aonedrive-alphabetics-27774257/index.html
https://storage.googleapis.com/aonedrive-antireform-915964604/index.html
https://storage.googleapis.com/aonedrive-apprehensiveness-182959460/index.html
https://storage.googleapis.com/aonedrive-arduousness-18101419/index.html
https://storage.googleapis.com/aonedrive-assentive-604684136/index.html
https://storage.googleapis.com/aonedrive-augmentationer-535444778/index.html
https://storage.googleapis.com/aonedrive-autopticity-986043285/index.html
https://storage.googleapis.com/aonedrive-baguets-663458386/index.html
https://storage.googleapis.com/aonedrive-balandrana-558153244/index.html
https://storage.googleapis.com/aonedrive-bcf-938708783/index.html
https://storage.googleapis.com/aonedrive-bedral-93343114/index.html
https://storage.googleapis.com/aonedrive-bedwarfed-855871520/index.html
https://storage.googleapis.com/aonedrive-blasts-285916956/index.html
https://storage.googleapis.com/aonedrive-bluejays-78351192/index.html
https://storage.googleapis.com/aonedrive-bogged-684855122/index.html
https://storage.googleapis.com/aonedrive-bugling-853293723/index.html
https://storage.googleapis.com/aonedrive-burnside-382555525/index.html
https://storage.googleapis.com/aonedrive-caboose-670706297/index.html
https://storage.googleapis.com/aonedrive-calving-566435066/index.html
https://storage.googleapis.com/aonedrive-camorra-235128019/index.html
https://storage.googleapis.com/aonedrive-caravansary-957206943/index.html
https://storage.googleapis.com/aonedrive-carets-982217477/index.html
https://storage.googleapis.com/aonedrive-castor-482130484/index.html
https://storage.googleapis.com/aonedrive-cherisher-881557007/index.html
https://storage.googleapis.com/aonedrive-chinks-89974884/index.html
https://storage.googleapis.com/aonedrive-chorizontes-780321770/index.html
https://storage.googleapis.com/aonedrive-coapostate-419147498/index.html
https://storage.googleapis.com/aonedrive-commiserated-365767546/index.html
https://storage.googleapis.com/aonedrive-congreso-48609305/index.html
https://storage.googleapis.com/aonedrive-cormus-254785729/index.html
https://storage.googleapis.com/aonedrive-counterwall-818465552/GMA.html
https://storage.googleapis.com/aonedrive-counterwall-818465552/index.html
https://storage.googleapis.com/aonedrive-dacryolithiasis-276136925/index.html
https://storage.googleapis.com/aonedrive-deadrize-281419705/index.html
https://storage.googleapis.com/aonedrive-decandrous-77175843/index.html
https://storage.googleapis.com/aonedrive-denaturized-404931663/index.html
https://storage.googleapis.com/aonedrive-deterration-600712631/index.html
https://storage.googleapis.com/aonedrive-discontentedness-316029959/index.html
https://storage.googleapis.com/aonedrive-dragonwort-161011487/index.html
https://storage.googleapis.com/aonedrive-dulceness-558544227/index.html
https://storage.googleapis.com/aonedrive-edgewise-982565100/index.html
https://storage.googleapis.com/aonedrive-elzevirian-175080952/index.html
https://storage.googleapis.com/aonedrive-endangium-608808007/index.html
https://storage.googleapis.com/aonedrive-enormity-685673847/index.html
https://storage.googleapis.com/aonedrive-epitomizer-25575182/index.html
https://storage.googleapis.com/aonedrive-excaudate-991117245/index.html
https://storage.googleapis.com/aonedrive-exoticalness-775726008/index.html
https://storage.googleapis.com/aonedrive-explorable-87849371/index.html
https://storage.googleapis.com/aonedrive-expositional-677137819/index.html
https://storage.googleapis.com/aonedrive-eyeshield-894238745/index.html
https://storage.googleapis.com/aonedrive-feijoa-893810390/index.html
https://storage.googleapis.com/aonedrive-flatterdock-271538507/index.html
https://storage.googleapis.com/aonedrive-foreswearing-792667147/index.html
https://storage.googleapis.com/aonedrive-fraughtage-593416166/index.html
https://storage.googleapis.com/aonedrive-fricatives-487330111/GMA.html
https://storage.googleapis.com/aonedrive-gallicism-751349753/index.html
https://storage.googleapis.com/aonedrive-gentianales-759124982/index.html
https://storage.googleapis.com/aonedrive-gingerbready-306608824/index.html
https://storage.googleapis.com/aonedrive-goaty-656585769/index.html
https://storage.googleapis.com/aonedrive-grout-504823117/index.html
https://storage.googleapis.com/aonedrive-halicore-344494914/index.html
https://storage.googleapis.com/aonedrive-hardball-129694529/index.html
https://storage.googleapis.com/aonedrive-headend-975918928/index.html
https://storage.googleapis.com/aonedrive-headlighting-336892906/index.html
https://storage.googleapis.com/aonedrive-hematuric-498815341/index.html
https://storage.googleapis.com/aonedrive-herbarizing-640769786/index.html
https://storage.googleapis.com/aonedrive-heteromita-856081356/index.html
https://storage.googleapis.com/aonedrive-historiography-349378319/index.html
https://storage.googleapis.com/aonedrive-hoicking-839882903/index.html
https://storage.googleapis.com/aonedrive-homalocenchrus-689591784/index.html
https://storage.googleapis.com/aonedrive-husklike-361308956/index.html
https://storage.googleapis.com/aonedrive-hydrophytous-874652875/index.html
https://storage.googleapis.com/aonedrive-hyperthrombinemia-404994945/index.html
https://storage.googleapis.com/aonedrive-infancy-397602010/index.html
https://storage.googleapis.com/aonedrive-infects-946372290/index.html
https://storage.googleapis.com/aonedrive-inflectionally-49762713/index.html
https://storage.googleapis.com/aonedrive-infratracheal-185932389/index.html
https://storage.googleapis.com/aonedrive-infusion-799252943/index.html
https://storage.googleapis.com/aonedrive-inkings-939294971/index.html
https://storage.googleapis.com/aonedrive-intercolonize-578556431/index.html
https://storage.googleapis.com/aonedrive-intitles-164253084/index.html
https://storage.googleapis.com/aonedrive-intoxicantly-399626327/index.html
https://storage.googleapis.com/aonedrive-ironfisted-159139883/index.html
https://storage.googleapis.com/aonedrive-lacunulose-247738593/index.html
https://storage.googleapis.com/aonedrive-lokaose-380207974/index.html
https://storage.googleapis.com/aonedrive-mararie-512902054/index.html
https://storage.googleapis.com/aonedrive-mechanophobia-972295231/index.html
https://storage.googleapis.com/aonedrive-mesocolons-554552970/index.html
https://storage.googleapis.com/aonedrive-moderators-571682914/index.html
https://storage.googleapis.com/aonedrive-monkeyshines-515821439/index.html
https://storage.googleapis.com/aonedrive-mysticetous-944074575/index.html
https://storage.googleapis.com/aonedrive-needlepoint-395861145/index.html
https://storage.googleapis.com/aonedrive-needy-609260547/index.html
https://storage.googleapis.com/aonedrive-nisan-359520855/index.html
https://storage.googleapis.com/aonedrive-noninterventional-458092185/index.html
https://storage.googleapis.com/aonedrive-nonjurable-217043350/index.html
https://storage.googleapis.com/aonedrive-objectize-495880124/index.html
https://storage.googleapis.com/aonedrive-oratress-857054919/index.html
https://storage.googleapis.com/aonedrive-ordinaries-765073335/index.html
https://storage.googleapis.com/aonedrive-orthopter-341356245/index.html
https://storage.googleapis.com/aonedrive-oscules-961962752/index.html
https://storage.googleapis.com/aonedrive-outmated-597454671/index.html
https://storage.googleapis.com/aonedrive-overpack-808020500/index.html
https://storage.googleapis.com/aonedrive-oversceptically-358429501/index.html
https://storage.googleapis.com/aonedrive-paindemaine-212603918/index.html
https://storage.googleapis.com/aonedrive-patheticalness-258886154/index.html
https://storage.googleapis.com/aonedrive-photoprocess-930872614/index.html
https://storage.googleapis.com/aonedrive-plauenite-16000608/index.html
https://storage.googleapis.com/aonedrive-pleurocera-937845450/index.html
https://storage.googleapis.com/aonedrive-polypaged-567962509/index.html
https://storage.googleapis.com/aonedrive-preaccused-375848328/index.html
https://storage.googleapis.com/aonedrive-precommuning-778000534/index.html
https://storage.googleapis.com/aonedrive-predisciplining-593667636/index.html
https://storage.googleapis.com/aonedrive-preprudently-539877250/index.html
https://storage.googleapis.com/aonedrive-prestress-810470960/index.html
https://storage.googleapis.com/aonedrive-primatological-303216596/index.html
https://storage.googleapis.com/aonedrive-professorships-810793099/index.html
https://storage.googleapis.com/aonedrive-psoroid-809974430/index.html
https://storage.googleapis.com/aonedrive-publicness-189469478/index.html
https://storage.googleapis.com/aonedrive-pudendum-660198270/index.html
https://storage.googleapis.com/aonedrive-punicine-326415881/index.html
https://storage.googleapis.com/aonedrive-purpense-651133867/index.html
https://storage.googleapis.com/aonedrive-rampsman-461831039/index.html
https://storage.googleapis.com/aonedrive-reded-832791965/index.html
https://storage.googleapis.com/aonedrive-reimbark-880908550/index.html
https://storage.googleapis.com/aonedrive-resale-417471916/index.html
https://storage.googleapis.com/aonedrive-reseiser-765602504/index.html
https://storage.googleapis.com/aonedrive-resoled-861329362/index.html
https://storage.googleapis.com/aonedrive-rhodymenia-415293747/index.html
https://storage.googleapis.com/aonedrive-rockabye-356100372/index.html
https://storage.googleapis.com/aonedrive-rottenstone-656698685/index.html
https://storage.googleapis.com/aonedrive-salar-965123760/index.html
https://storage.googleapis.com/aonedrive-sb-982963294/index.html
https://storage.googleapis.com/aonedrive-scouch-22913829/index.html
https://storage.googleapis.com/aonedrive-scuff-488469257/GMA.html
https://storage.googleapis.com/aonedrive-septennate-874641566/index.html
https://storage.googleapis.com/aonedrive-serendipitously-696361534/index.html
https://storage.googleapis.com/aonedrive-shahid-395480616/index.html
https://storage.googleapis.com/aonedrive-sherpas-428731583/index.html
https://storage.googleapis.com/aonedrive-shilloo-709296907/index.html
https://storage.googleapis.com/aonedrive-shraf-70183863/index.html
https://storage.googleapis.com/aonedrive-smaze-11720893/index.html
https://storage.googleapis.com/aonedrive-snappishly-440461286/index.html
https://storage.googleapis.com/aonedrive-spahis-109494121/index.html
https://storage.googleapis.com/aonedrive-spaned-18785768/index.html
https://storage.googleapis.com/aonedrive-sporicide-256067498/index.html
https://storage.googleapis.com/aonedrive-st-126309915/index.html
https://storage.googleapis.com/aonedrive-stangs-359056843/index.html
https://storage.googleapis.com/aonedrive-stretchier-69603610/index.html
https://storage.googleapis.com/aonedrive-substitutively-520756295/index.html
https://storage.googleapis.com/aonedrive-summat-902591729/index.html
https://storage.googleapis.com/aonedrive-surebutted-512628106/index.html
https://storage.googleapis.com/aonedrive-surfing-45472804/index.html
https://storage.googleapis.com/aonedrive-swinepox-620935803/index.html
https://storage.googleapis.com/aonedrive-tableted-810457961/index.html
https://storage.googleapis.com/aonedrive-tagbanua-299872169/index.html
https://storage.googleapis.com/aonedrive-tapiocas-519232375/index.html
https://storage.googleapis.com/aonedrive-tasbih-350645076/index.html
https://storage.googleapis.com/aonedrive-teazling-497668683/index.html
https://storage.googleapis.com/aonedrive-tetrasyllable-407561175/index.html
https://storage.googleapis.com/aonedrive-toadishness-466955951/index.html
https://storage.googleapis.com/aonedrive-towline-85336607/index.html
https://storage.googleapis.com/aonedrive-traditionately-864162359/index.html
https://storage.googleapis.com/aonedrive-tres-980865941/index.html
https://storage.googleapis.com/aonedrive-tribromphenol-792342015/index.html
https://storage.googleapis.com/aonedrive-tricosane-371236858/index.html
https://storage.googleapis.com/aonedrive-trilinolate-200784667/index.html
https://storage.googleapis.com/aonedrive-truce-890790758/index.html
https://storage.googleapis.com/aonedrive-unechoing-362171070/index.html
https://storage.googleapis.com/aonedrive-unfertilizing-495645174/index.html
https://storage.googleapis.com/aonedrive-unifier-417396273/index.html
https://storage.googleapis.com/aonedrive-unknightly-310026459/index.html
https://storage.googleapis.com/aonedrive-unpacified-865573173/index.html
https://storage.googleapis.com/aonedrive-unvoraciousness-152827706/index.html
https://storage.googleapis.com/aonedrive-upleaps-901875380/index.html
https://storage.googleapis.com/aonedrive-vaccinations-547858314/index.html
https://storage.googleapis.com/aonedrive-viburnums-489683753/index.html
https://storage.googleapis.com/aonedrive-woolwich-430845733/index.html
https://storage.googleapis.com/aonedrive-ziamet-18523709/index.html
https://storage.googleapis.com/aourtime-slang-614188345/index.html
https://storage.googleapis.com/aoutlook-airsheds-1659273/index.html
https://storage.googleapis.com/aoutlook-amniorrhea-17875895/index.html
https://storage.googleapis.com/aoutlook-amniorrhea-17875895/index.html?email=
https://storage.googleapis.com/aoutlook-amniorrhea-17875895/index.html?email=du.tran@ladwp.com
https://storage.googleapis.com/aoutlook-antitubercular-297922690/index.html
https://storage.googleapis.com/aoutlook-antitubercular-297922690/index.html?l=_JeHFUq_VJOXK0QWHtoGYDw_Product-UserID&
https://storage.googleapis.com/aoutlook-calices-362826399/index.html
https://storage.googleapis.com/aoutlook-concordatum-329285300/index.html
https://storage.googleapis.com/aoutlook-cytosines-737408570/index.html
https://storage.googleapis.com/aoutlook-cytosines-737408570/index.html?email=jkal%40abc.edu
https://storage.googleapis.com/aoutlook-cytosines-737408570/index.html?email=jkal@abc.edu
https://storage.googleapis.com/aoutlook-cytosines-737408570/index.html?email=larry.dobbe@marinecu.com&c=E,1,D-mbr8j2aMXCSvaFnTpZnMlmqeu9Mm_CK_MgNfsaI0D25UFam8VcpGt5S2r8oJzbSPxLFeZG3iK1pS8DypW47BwAkUZ3wGrsqTbDjP0-uVcGxA,,&typo=1
https://storage.googleapis.com/aoutlook-fibrin-402116448/index.html
https://storage.googleapis.com/aoutlook-forespoke-681205456/index.html
https://storage.googleapis.com/aoutlook-hydrophthalmus-376610461/index.html
https://storage.googleapis.com/aoutlook-misspender-917867772/index.html
https://storage.googleapis.com/aoutlook-outbelch-317321136/index.html
https://storage.googleapis.com/aoutlook-phalangigrady-490790886/index.html
https://storage.googleapis.com/aoutlook-phylloquinone-627593835/index.html
https://storage.googleapis.com/aoutlook-platilla-256443704/index.html
https://storage.googleapis.com/aoutlook-preduplicate-726628519/index.html
https://storage.googleapis.com/aoutlook-reblame-686061315/index.html
https://storage.googleapis.com/aoutlook-scotist-58775533/index.html
https://storage.googleapis.com/aoutlook-streptococcic-425450888/index.html
https://storage.googleapis.com/aoutlook-superindependence-988939402/index.html
https://storage.googleapis.com/asharepoint-administerd-494241918/index.html
https://storage.googleapis.com/asharepoint-aldide-162229156/index.html
https://storage.googleapis.com/asharepoint-alguazil-546672817/index.html
https://storage.googleapis.com/asharepoint-antecornu-664068425/index.html
https://storage.googleapis.com/asharepoint-bahaism-329751662/index.html
https://storage.googleapis.com/asharepoint-bedwarfed-630874609/index.html
https://storage.googleapis.com/asharepoint-bheestie-424668813/index.html
https://storage.googleapis.com/asharepoint-bilifuscin-626677178/index.html
https://storage.googleapis.com/asharepoint-camoufleurs-292615000/index.html
https://storage.googleapis.com/asharepoint-cantinas-124280312/index.html
https://storage.googleapis.com/asharepoint-cheefullest-499592064/index.html
https://storage.googleapis.com/asharepoint-chemigrapher-165606140/index.html
https://storage.googleapis.com/asharepoint-chertier-740548631/index.html
https://storage.googleapis.com/asharepoint-clerkless-613571659/index.html
https://storage.googleapis.com/asharepoint-collaborations-118508658/index.html
https://storage.googleapis.com/asharepoint-contumacity-608511750/index.html
https://storage.googleapis.com/asharepoint-conyrin-926061061/index.html
https://storage.googleapis.com/asharepoint-cotan-861417547/index.html
https://storage.googleapis.com/asharepoint-culicidal-430475587/index.html
https://storage.googleapis.com/asharepoint-digammic-188079063/index.html
https://storage.googleapis.com/asharepoint-ditone-218507008/index.html
https://storage.googleapis.com/asharepoint-endothecal-770213536/index.html
https://storage.googleapis.com/asharepoint-ephoralty-477195865/index.html
https://storage.googleapis.com/asharepoint-ernes-819852795/index.html
https://storage.googleapis.com/asharepoint-evangelicalism-237159924/index.html
https://storage.googleapis.com/asharepoint-furnacite-388025745/index.html
https://storage.googleapis.com/asharepoint-gypping-328999040/index.html
https://storage.googleapis.com/asharepoint-hypersthenic-66001060/index.html
https://storage.googleapis.com/asharepoint-icecap-332691270/index.html
https://storage.googleapis.com/asharepoint-imbased-430818157/index.html
https://storage.googleapis.com/asharepoint-imbased-430818157/office365.html
https://storage.googleapis.com/asharepoint-impoundments-656771807/index.html
https://storage.googleapis.com/asharepoint-indictment-371683276/index.html
https://storage.googleapis.com/asharepoint-inflator-823748771/index.html
https://storage.googleapis.com/asharepoint-iniquity-36280337/index.html
https://storage.googleapis.com/asharepoint-ironhard-651083774/index.html
https://storage.googleapis.com/asharepoint-kingcraft-970290823/index.html
https://storage.googleapis.com/asharepoint-limequat-939454772/index.html
https://storage.googleapis.com/asharepoint-lombardeer-949072087/index.html
https://storage.googleapis.com/asharepoint-louverwork-241693326/index.html
https://storage.googleapis.com/asharepoint-lulu-216223739/index.html
https://storage.googleapis.com/asharepoint-luncheonette-427212214/index.html
https://storage.googleapis.com/asharepoint-marspiter-115190738/index.html
https://storage.googleapis.com/asharepoint-mas-71412682/index-home.html
https://storage.googleapis.com/asharepoint-mas-71412682/index.html
https://storage.googleapis.com/asharepoint-matin-94941045/index.html
https://storage.googleapis.com/asharepoint-mckay-647458921/index.html
https://storage.googleapis.com/asharepoint-morselling-411198998/index.html
https://storage.googleapis.com/asharepoint-nonactual-854693401/index.html
https://storage.googleapis.com/asharepoint-overintensity-398891543/index.html
https://storage.googleapis.com/asharepoint-overthrow-373848197/index.html
https://storage.googleapis.com/asharepoint-paleostriatum-235549097/GMA.html
https://storage.googleapis.com/asharepoint-paleostriatum-235549097/index.html
https://storage.googleapis.com/asharepoint-preservation-639916604/index.html
https://storage.googleapis.com/asharepoint-processability-372658922/index.html
https://storage.googleapis.com/asharepoint-professionalized-217274199/index.html
https://storage.googleapis.com/asharepoint-prospers-214761571/GMA.html
https://storage.googleapis.com/asharepoint-prospers-214761571/OTHER.html
https://storage.googleapis.com/asharepoint-prospers-214761571/index.html
https://storage.googleapis.com/asharepoint-prytanis-664622039/index.html
https://storage.googleapis.com/asharepoint-querendy-217445447/index.html
https://storage.googleapis.com/asharepoint-reemerged-832444337/index.html
https://storage.googleapis.com/asharepoint-repentingly-582099050/index.html
https://storage.googleapis.com/asharepoint-retables-254025698/index.html
https://storage.googleapis.com/asharepoint-rhythmed-469904318/GMA.html
https://storage.googleapis.com/asharepoint-rhythmed-469904318/index.html
https://storage.googleapis.com/asharepoint-salacity-249514965/index.html
https://storage.googleapis.com/asharepoint-sapotilla-292433271/index.html
https://storage.googleapis.com/asharepoint-sempstrywork-885252390/index.html
https://storage.googleapis.com/asharepoint-situal-621074413/index.html
https://storage.googleapis.com/asharepoint-stepmother-292798376/index.html
https://storage.googleapis.com/asharepoint-stowwood-70637085/index.html
https://storage.googleapis.com/asharepoint-superattraction-824588173/index.html
https://storage.googleapis.com/asharepoint-supraocclusion-842081082/index.html
https://storage.googleapis.com/asharepoint-unactually-915091686/index.html
https://storage.googleapis.com/asharepoint-unbankableness-683730596/index.html
https://storage.googleapis.com/asharepoint-uncrossexaminable-477414226/index.html
https://storage.googleapis.com/asharepoint-uncrusted-341264945/index.html
https://storage.googleapis.com/asharepoint-unentreating-317749122/index.html
https://storage.googleapis.com/asharepoint-unexaggerated-584193481/index.html
https://storage.googleapis.com/asharepoint-unjoinable-416419306/index.html
https://storage.googleapis.com/asharepoint-unsatiricalness-901161534/index.html
https://storage.googleapis.com/asharepoint-unserene-134830614/index.html
https://storage.googleapis.com/asharepoint-upbear-998421198/index.html
https://storage.googleapis.com/asharepoint-visitor-783447426/index.html
https://storage.googleapis.com/asharepoint-weirdwoman-991244860/index.html
https://storage.googleapis.com/asharepoint-zosteropinae-343847169/index.html
https://storage.googleapis.com/aunique-cardiopuncture-795184203/index.html?access=lalala@gmail.com
https://storage.googleapis.com/awebmail-adiaphanousness-991703013/index2.html
https://storage.googleapis.com/bp-windows/owa-outlook.htm
https://storage.googleapis.com/chinn1/chinuu.htm.html
https://storage.googleapis.com/dirowa22/akzm.htm
https://storage.googleapis.com/myofficesbucket/redirect-onedrive-document-eml-365.html
https://storage.googleapis.com/myowamail/live.htm
https://storage.googleapis.com/myowamail/live.htm?email
https://storage.googleapis.com/myowamail/live.htm?email=janelva.williams@ladwp.com
https://storage.googleapis.com/myowamail/owaprofile.htm
https://storage.googleapis.com/myowamail/window.htm
https://storage.googleapis.com/myowamail/window.htm?email=
https://storage.googleapis.com/myowamail/window.htm?email=email@domain.tld
https://storage.googleapis.com/myowamail/window.htm?email=fuckyou@asshole.com
https://storage.googleapis.com/myowamail/window.htm?email=iheart@kyledavis.com
https://storage.googleapis.com/myowamail/window.htm?email=nobody@mycraftmail.com
https://storage.googleapis.com/odo1/ind.html
https://storage.googleapis.com/office-document-2314312/fileid/businessmodelsbusinessstrategy.pdf
https://storage.googleapis.com/owalive/Window.htm
https://storage.googleapis.com/owalive/live.htm
https://storage.googleapis.com/owalive/owa.htm
https://storage.googleapis.com/owoxo/lives.htm?email=test@test.com
https://storage.googleapis.com/owoxo/lives.htm?email=tracey.glover@jetstar.com
https://storage.googleapis.com/owoxo/win.htm
https://storage.googleapis.com/owoxo/window.htm?email=rebecca.milne@futurefund.gov.au
https://storage.googleapis.com/rich-owo/win.htm