Muni Hosting: A safe haven for phishing and credit card fraud
Muni Hosting is a boutique bulletproof server hosting provider knee-deep in running phishing scams, SIM swapping attacks and bank fraud. My latest research takes an attempt at mapping the scale of the operation and identify the perpetrator behind these illegal acts.
The First Batch of Domains
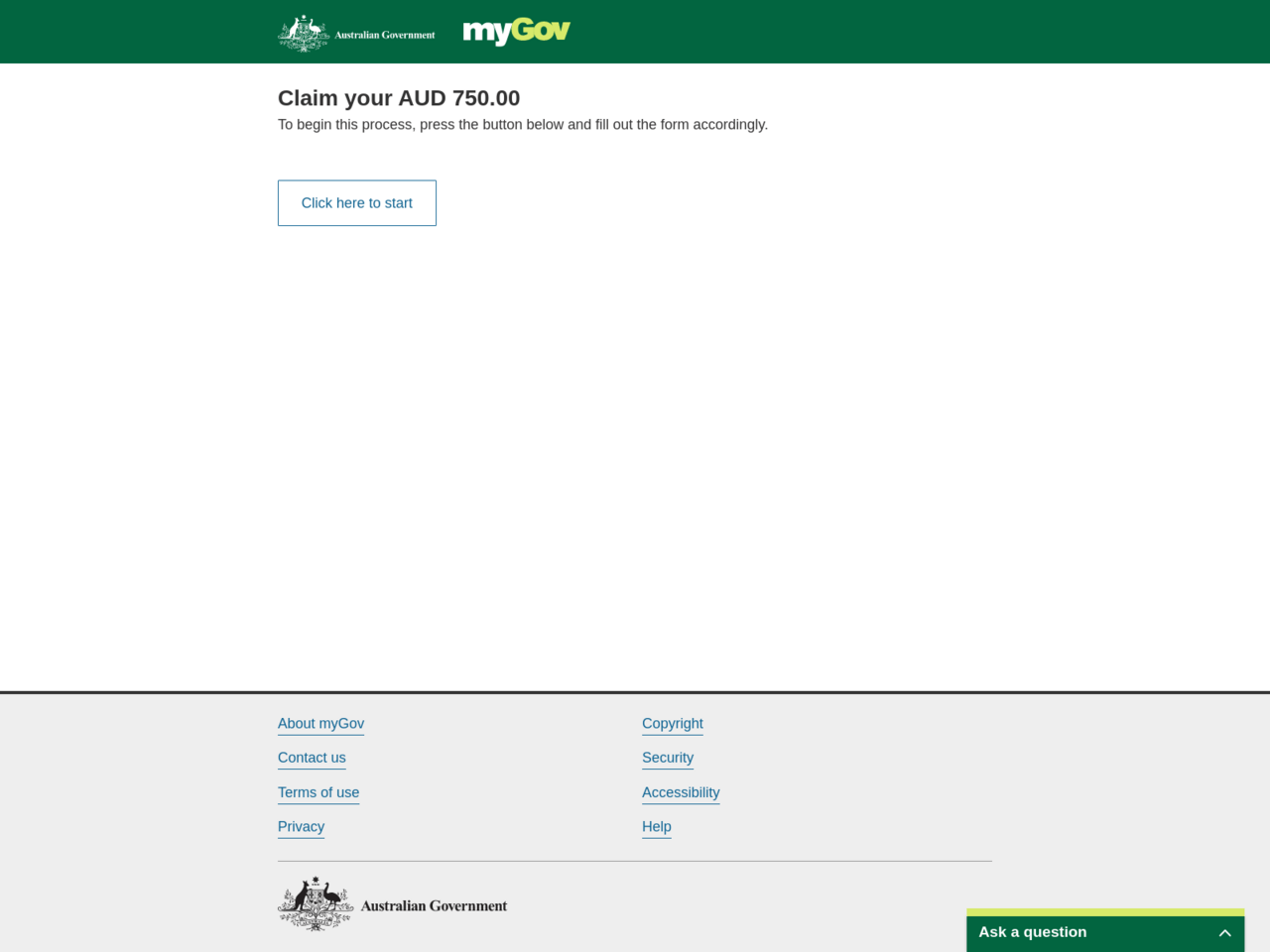
The starting point of this research was a website impersonating the Australian Taxation Office (ATO). The page that was running on ato-verify.com was trying to steal the victims’ login credentials to the Australian myGov portal.
It turns out that the page was hosted on a web server on 111.90.150.212 in Malaysia belonging to the virtual server hosting provider named Shinjiru Technology.
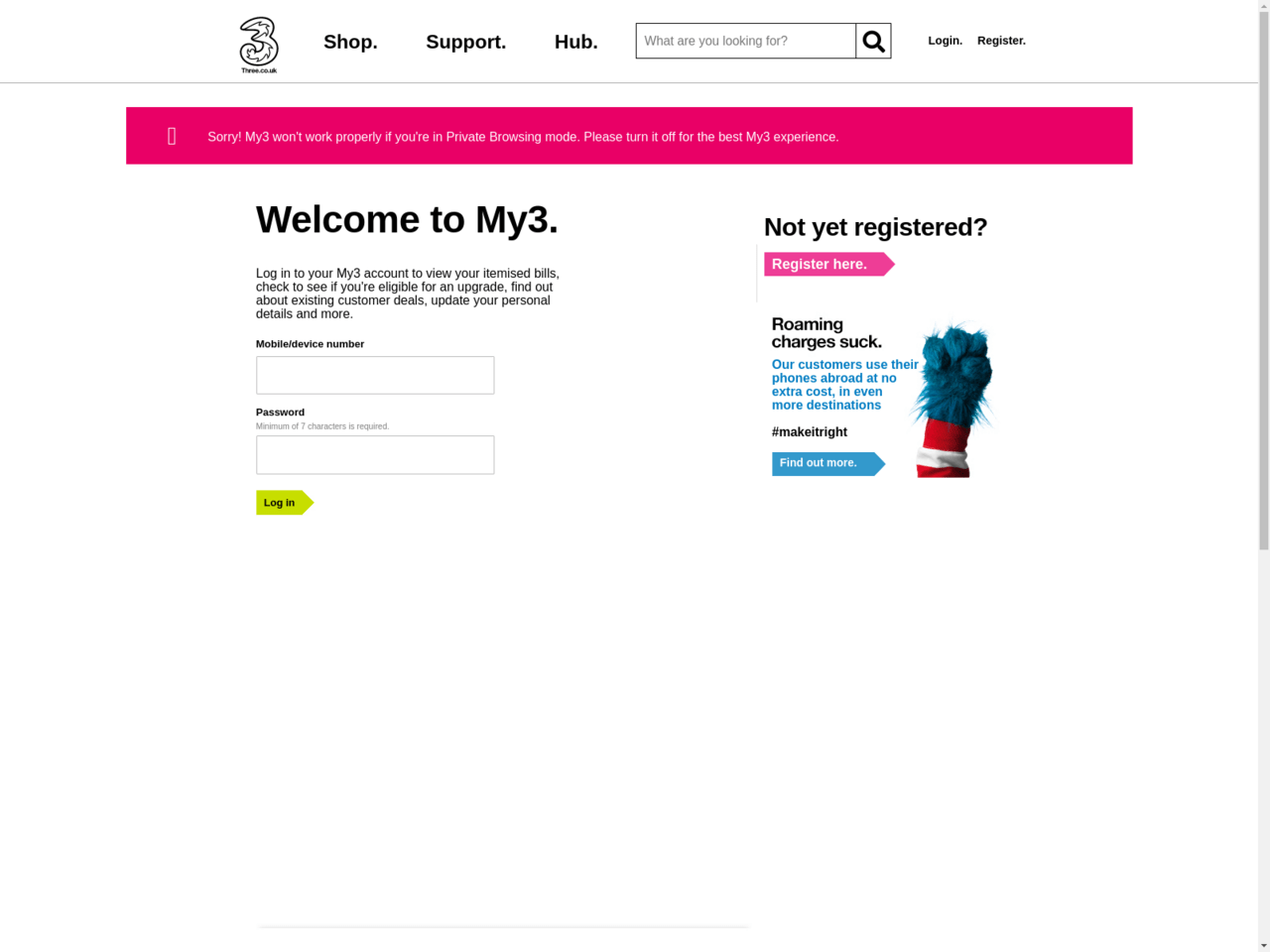
By pivoting on this IP address and other indicators, I found a handful of domain names also associated with similar phishing scams targeting victims in Australia as well as in the UK.
3help.support-helpcentre.com
accountalertservices.com
amzn-security.com
ato-secure-account.com
ato-verify.com
avtonavigator.net
betaalplatform.icu
bill-auth.com
bill417.com
billing-vz1-services.com
covid-19.mygovauss.com
covid19.mygovauss.com
edca888.com
ee-bills.co.uk
ee-securesite.com
granf919.com
hmrcvalidation.com
hoesoutlet888.com
muni-hosting.com
my3-billing-verification.com
my3.account.bill-auth.com
my3.bill-auth.com
my3.secure.verify-portal.com
my3.service.bill-auth.com
my3.validate-acc.com
my3alert-service.com
my3alerts-service.com
my3-solution.com
mybilling3.com
myee-uksupport.com
mygovauss.com
mythree-authenticate.com
mythreeacount-verify.com
mythreesecureuk.com
natwestsupportuk.com
ordermbtshoes.com
rebategovuk.com
recent-transaction-help.com
rententionteam-ee.com
serverhsbcprotocoldepartments.com
speed.angkey37.com
support-helpcentre.com
support-pypal.com
supporteebilling.com
supportvzdepartment.com
ukng756.com
ukrebates-revenue.com
uktaxrebates.com
validate-acc.com
verify-payment-netflix.com
verify-portal.com
verify-threeaccount.com
verify3-page.com
By looking at the domain names, most of them are targeting UK-based businesses such as Three and EE, two mobile phone providers. One of the domain name from the list resembles to NatWest, which is one of the major banks in the UK. Also, there are domains impersonating the tax office in the UK.
The Bulletproof Hosting Provider
What caught my eyes is one of the domains named muni-hosting.com, which turned out to be the hosting provider associated with these scams. Unfortunately, muni-hosting.com was down as the virtual server on 111.90.150.212 was shut down abruptly – but more about this later.
I found that several domains from above were moved to a different IP address at 101.99.90.155. By pivoting on this one, I was able to identify another batch of domain names also associated with Muni Hosting:
02-billing-verification.com
3threesupport.com
accounts-pay-pal-verification.com
amzn-secureinfoteam.com
bill430.com
billing-3verify.com
billing-telstra.com
checkmy3account.com
e-computers.net
fifth3rdlog-secureteam.com
gosweet.xyz
govuk-revenuehelp.com
hsbc-online-auth.com
my.three.update.bill430.com
muniservers.com
mybillingthree.com
myfservers.com
myoptus-billing.com
mythreeaccount-identification.com
mythreesecureuk.com
optus-billing.com
paypal-charities.com
reset-access.com
secure-paypl-account.com
spt-netflix.com
threemobilesupport.com
threepaybills.com
threeuk-alerts.com
usaa-secureinfoteam.com
usaa-securelogin.com
usaa-secureteam.com
verify-my3-billing.com
vodafone-billing.com
Most of these are mobile phone providers, such as Optus (AU), Telstra (AU), and Vodafone (UK/AU). Also, there is one UK bank on the list: HSBC.
More Domains
Some of these domains shared certain indicators, so I found that the following domain names are also likely to be related:
billing-3-support.com
ee-help-page.com
gov-application.com
my-ee-support.com
my-threelogin-account.com
my3-payments.com
my3-uksupport.com
my3mybilling.com
mybillingaccount.info
myee-helppage.com
mythree-unrestrict.com
ppl-billing-support.com
resolutiocentre.com
service-three.com
verify-mobile3.com
I also found this cluster that may or may not be associated with Muni Hosting:
assist-helpgb.com
assist-helpuk.com
cryptorelief.us
dbdesignit.com
divamaxlab.co
hmrctaxrefunder.com
ljemoliset.com
perferectoselecion.icu
por-segura.com
royalgoldboard.com
stillwavey.xyz
tax-rebate.me.uk
Who is Muni Hosting?
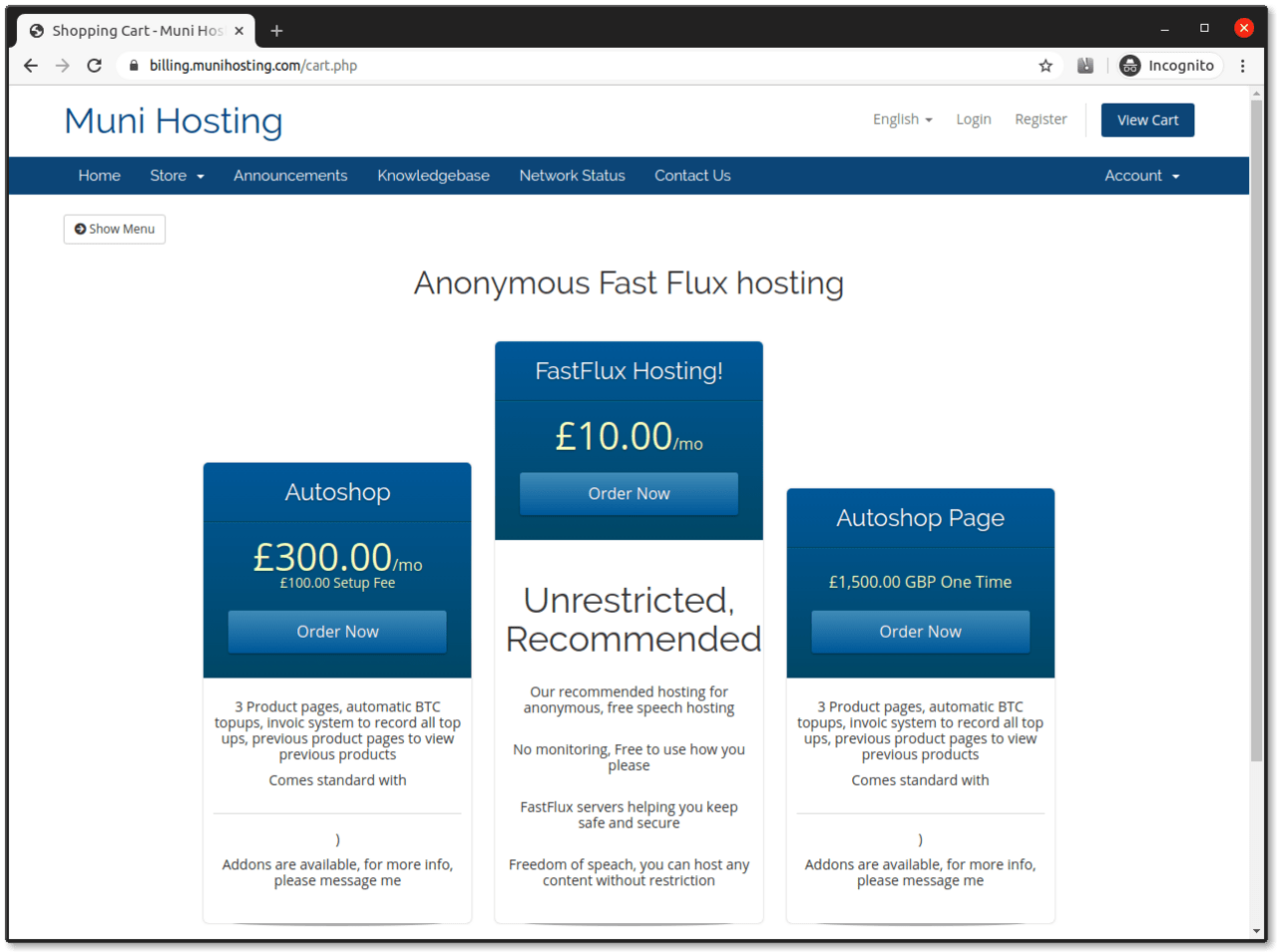
A large batch of domain names is closely associated with the aforementioned web hosting provider named Muni Hosting now running at munihosting.com.
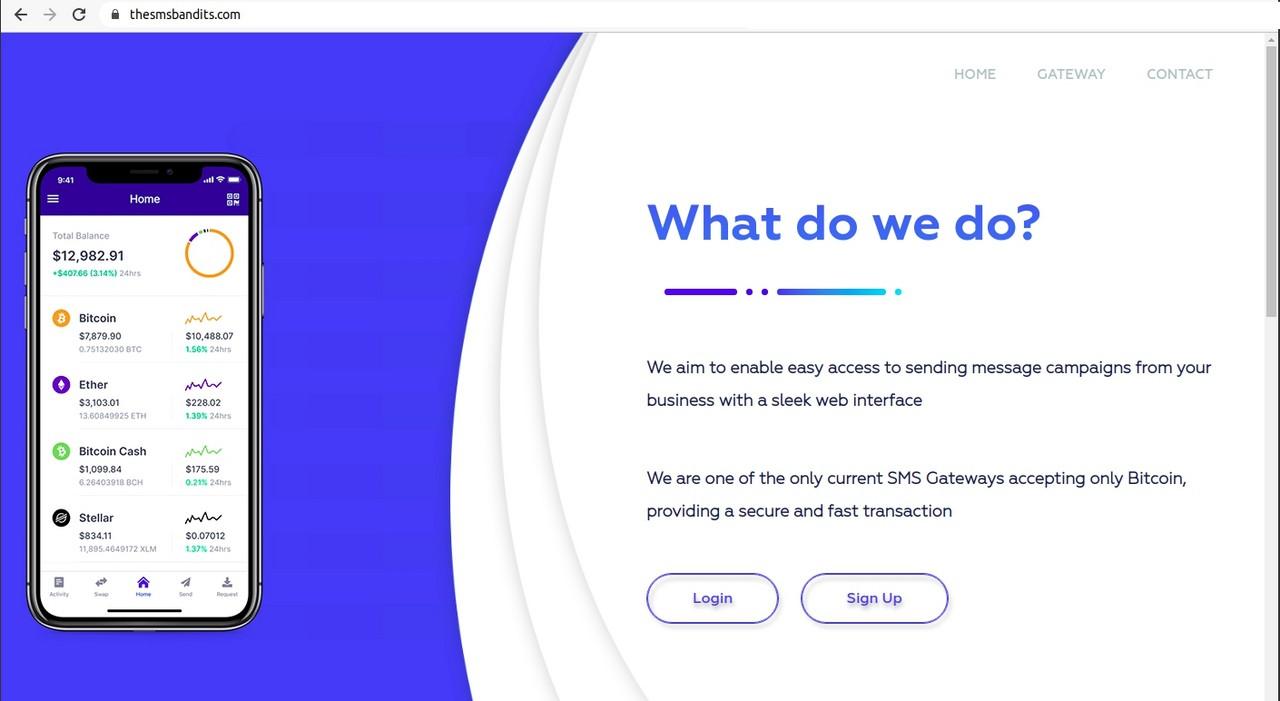
This provider is offering “anonymous, free speech hosting” and “fast-flux” services according to its website. On a related note, Fast flux is a technique commonly used by malware and phishing campaigns to avoid firewalls, blacklists and other counter-measures.
The fast-flux hosting boasts that “Freedom of speach (sic!), you can host any content without restriction” is one of the major highlights. This is nothing more than deception, as the service is merely a safe haven for scams rather than a genuine platform providing a platform for free speech.
The website was migrated from muni-hosting.com to munihosting.com recently.
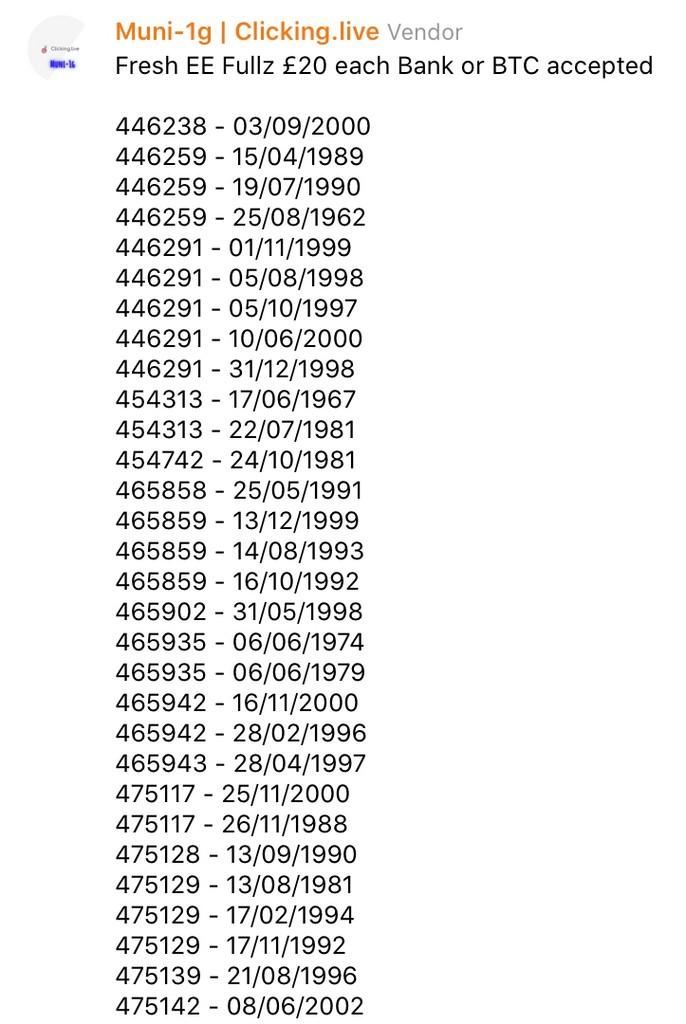
Muni’s other offerings include Autoshop, which is a commonly used name for platforms selling stolen credit card data.
According to certain indicators, Uncle Muni may be involved in alphashop.cc and clickin.click, both of them are marketplaces for buying and selling other people’s credit card details.
The Adversary Behind the Scam
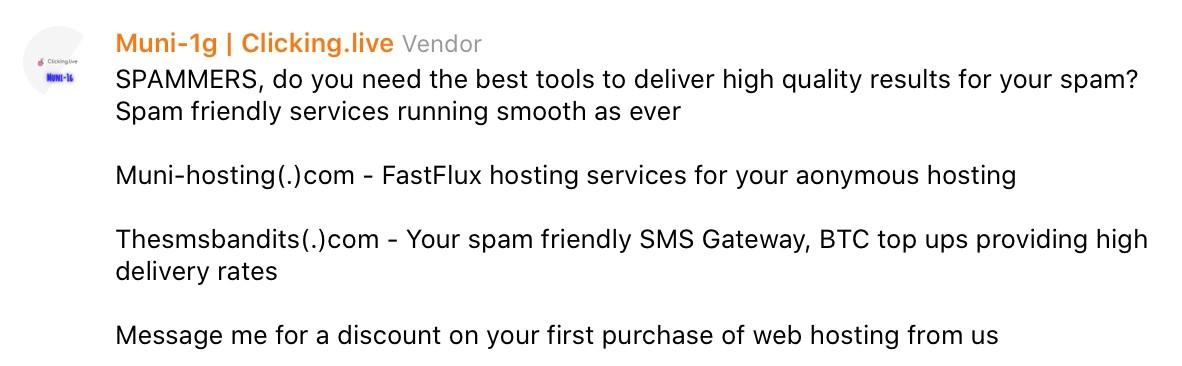
According to the website of Muni Hosting, the bulletproof services are provided by Uncle Muni. The perpetrator is also known as @Bamit9 on Telegram and has a WhatsApp account associated at +447933037077.
Uncle Muni is often seen on Telegram selling credit card and bank account login details along with his web hosting services.
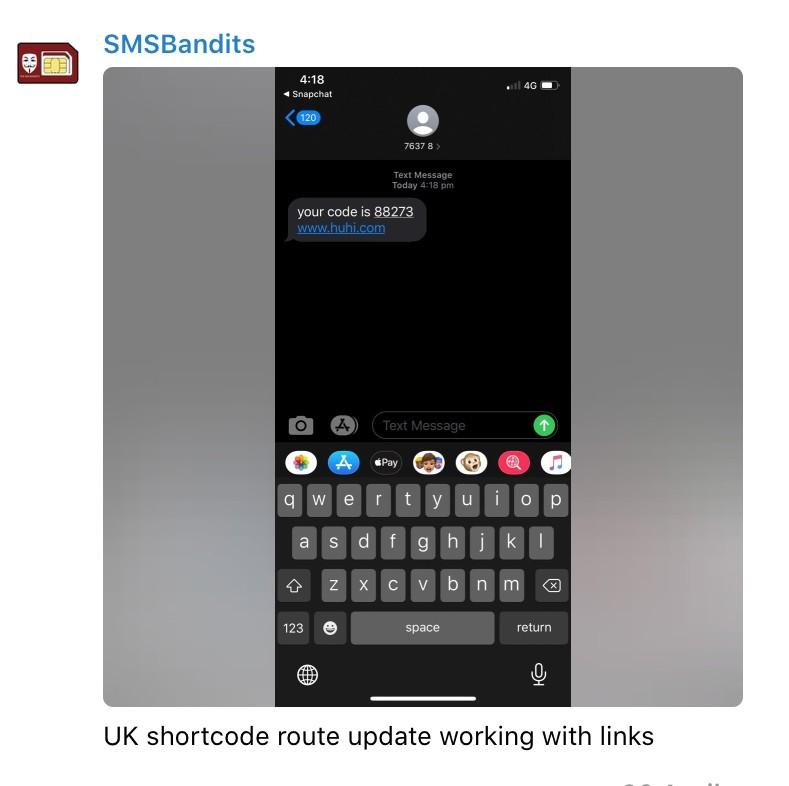
Uncle Muni also has a side-project named thesmsbandits.com offering text-message services meant for SMS-based phishing. The service is capable to send deceitful text messages with short phone numbers appear to be similar to legitimate SMS messages.
The innocently-looking website is just a facade hiding a full-blown SMS-based phishing machinery.
One of the feature highlights is the shortcode routes. It allows scammers to send text messages from legitimately-looking short phone numbers further increasing the success rates of phishing attacks.
Uncle Muni also offers his capabilities as a managed service. His anti-bot techniques are active countermeasures against security researchers trying to identify and take down phishing pages.
In summary, Uncle Muni appears to be using the combination of email and SMS phishing techniques combined with SIM swapping to steal credit card details and to drain bank accounts of his unsuspecting victims. As a side gig, Uncle Muni offers web hosting and the SMS services for those being in the same line of business.
Other Details
DNS name servers:
ns1.muniservers.com
ns2.muniservers.com
ns1.myfservers.com
ns2.myfservers.com
IP addresses:
101.99.90.155
111.90.142.136
111.90.150.159
111.90.150.212
13.248.196.204
157.245.38.210
167.71.78.187
185.218.235.113
209.182.193.140
209.99.64.76
216.157.88.24
35.246.3.36
70.39.249.157
WHOIS and contact email addresses:
26april1@protonmail.com
BusinessPromotion@protonmail.com
account1bargain@protonmail.com
ban@bill889.xyz
bill417@yopmail.com
bill430@yopmail.com
blobltio@protonmail.com
brianwhite1131@icloud.com
chop6969@protonmail.com
ctrappy2@gmail.com
dataspecialist@icloud.com
davormfc42@gmail.com
empirexd@protonmail.com
fastfluxhosting@gmail.com
fbandz1k@yandex.com
fpaysbills@gmail.com
franksinatra997@protonmail.com
ivyblue330@gmail.com
jaibains515@gmail.com
joelbrown112@yopmail.com
johnsmith@outlook.com
lucynickerson@yandex.com
matthewstevenson1@protonmail.com
matthewstevenson1@yahoo.com
motion100@mail.com
munihosting@protonmail.com
notification@kbreaders.com
nzt.matr.ic11@gmail.com
perfdjs09@protonmail.com
ramybultaif@outlook.com
slimezino@gmail.com
stackorstarvev2@gmail.com
support@unclemuni.com
tagmaker48@gmail.com
tdads0987ty@protonmail.com
time453@protonmail.com
tommyfree12@gmail.com
tryated64@gmail.com
Uncle Muni is frequently seen on:
t.me/clickinglivepublic
t.me/SMSBandits
Uncle Muni’s Telegram and Snapchat handles:
https://t.me/joinchat/AAAAAFXFVQ4sWAcKhJpozw (@Bamit9)
@muni-1g
@muni-1gv2
@muni-1gv2
@muni-1gv2
@muniwork
Possibly related social media profiles (unconfirmed):
https://www.tiktok.com/@unclemuni
https://www.instagram.com/unclemuni/
https://open.spotify.com/user/unclemuni
https://twitter.com/unclemuni
https://www.my.freelancer.com/u/unclemuni
https://www.nulled.to/user/3685261-unclemuni
https://tracr.co/user/519485622633627659
Based on these social media profiles, Uncle Muni is likely to be based in the UK.
What’s next?
After the publication of this post, the details have been passed on to Action Fraud, the national fraud and cyber crime reporting centre in the UK. A number of selected IOCs were submitted to Open Threat Exchange. Muni Hosting was also reported to the Australian Cyber Security Centre as some of the impersonated brands and victims are from Australia.
Update (20 June 2020): The websites associated with Muni Hosting are offline.